Saviynt Blog
Stay up to date on the latest identity security news, research and more.
Content Type
Industry
Solutions

05 / 28 / 2025
5 Ways to Solve Compliance Challenges with Saviynt’s Identity Security Platform
READ BLOG

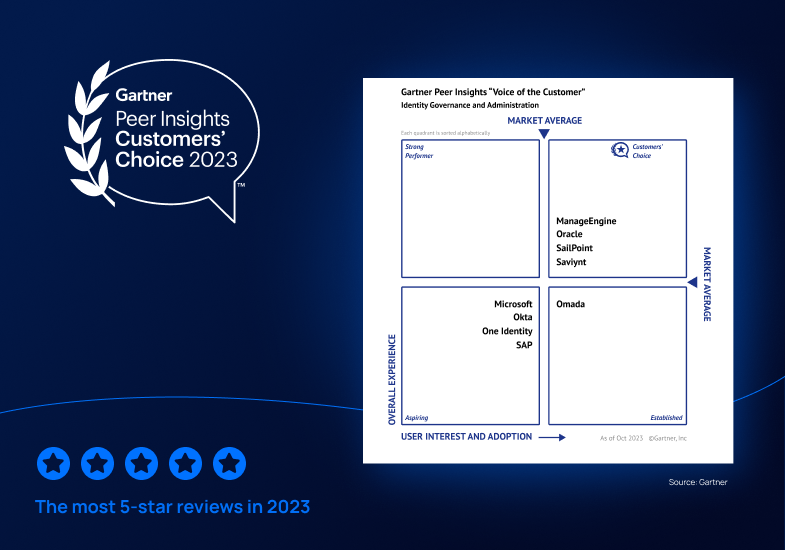
12 / 20 / 2023
Saviynt a Gartner® Peer Insights™ Customers' Choice in Identity Governance and Administration—Three Years in a Row
READ BLOG






















04 / 17 / 2023
Choosing a Cloud Privileged Access Management (PAM) Solution?: Three Must-Ask Questions
READ BLOG








12 / 13 / 2022
Saviynt EIC Scores 95/100 for Core Criteria in the 2022 Gartner® Solution Comparison for Identity Governance and Administration¹
READ BLOG





10 / 13 / 2022
New EIC v2022 Enhancements Boost Speed & Efficiency in Application Onboarding
READ BLOG








08 / 17 / 2022
3 Key IGA Modernization Must-Haves: All the Features, None of the Compromise
READ BLOG






07 / 06 / 2022
Top Challenges to Achieving Enterprise-Wide Visibility of Privileged Access
READ BLOG

06 / 09 / 2022
Gain Peace of Mind with Emergency Access Management & Out-of-the-Box Compliance Reporting
READ BLOG
06 / 02 / 2022
Solve Compliance Headaches with Cross-App Reporting and Automated Certification
READ BLOG

05 / 26 / 2022
Stop Remediation Burnout With Fine-Grained Controls and Out-of-the-Box Rulesets
READ BLOG











03 / 22 / 2022
Ask the Experts: Solving Top Multi-Cloud Identity Management & Governance Challenges
READ BLOG



11 / 19 / 2021
Getting GRC Right: Three Steps to Achieving Application Access Governance Maturity
READ BLOG
11 / 15 / 2021
Enterprise Identity Cloud: Accelerate Your Zero-Trust Journey with New Microsoft Integrations
READ BLOG