Secure Every Identity — Human and Non-Human
Discover all non-human identities, enriched with contextual insights.
.png?noresize&width=148&height=84&name=Untitled%20design%20(83).png)
Secure non-human identities from day one
Get a real-time inventory
Understand your identity security posture
Spot critical risks
Generate access map
Track lifecycle events
Accelerate remediation efforts
Extend identity security to non-human identities
Protect non-human identities from Day 1 with Saviynt Identity Cloud. Gain full visibility, contextual insights, and risk-based evaluation for non-human identities, just as you do for human identities without any additional integration effort. Secure all identities comprehensively and seamlessly throughout a single, unified identity security platform.
Gain a unified view of all NHIs and their security posture
Get a comprehensive, real-time inventory of your non-human identity landscape.
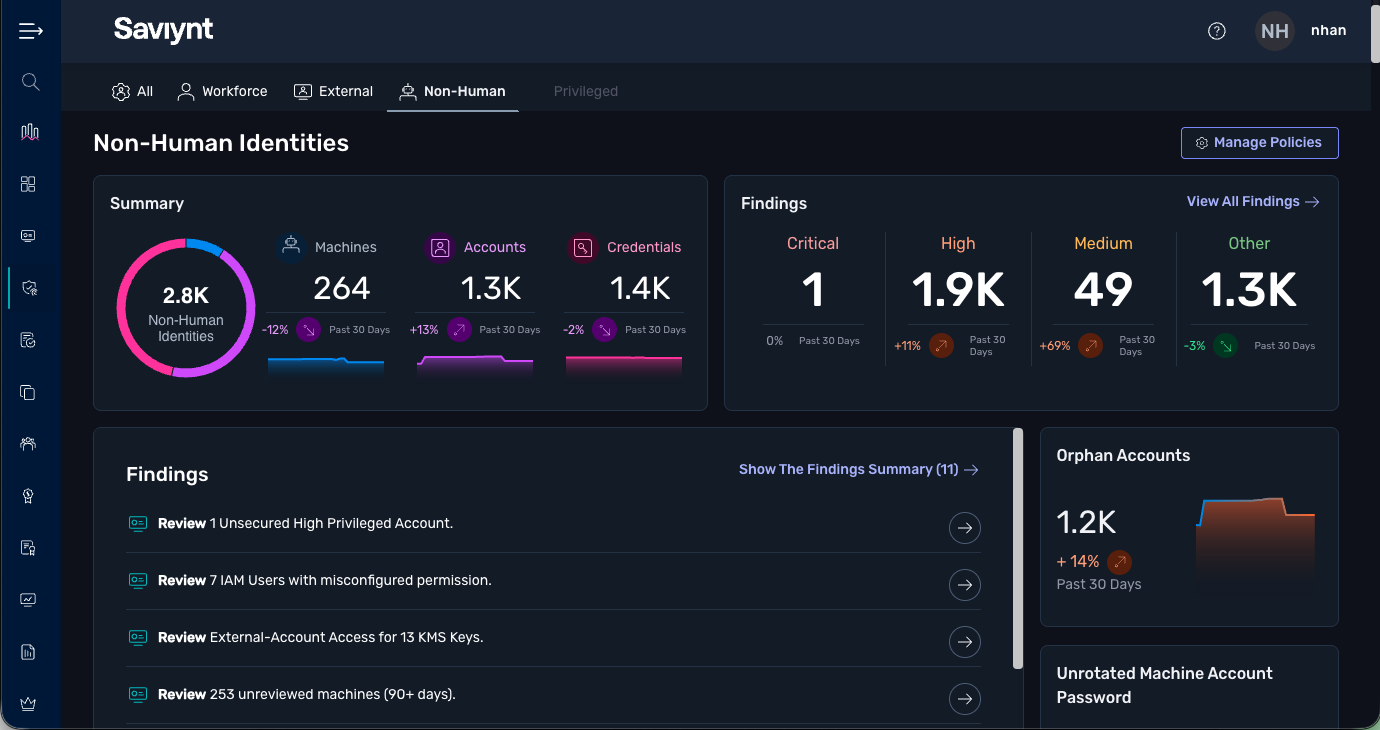
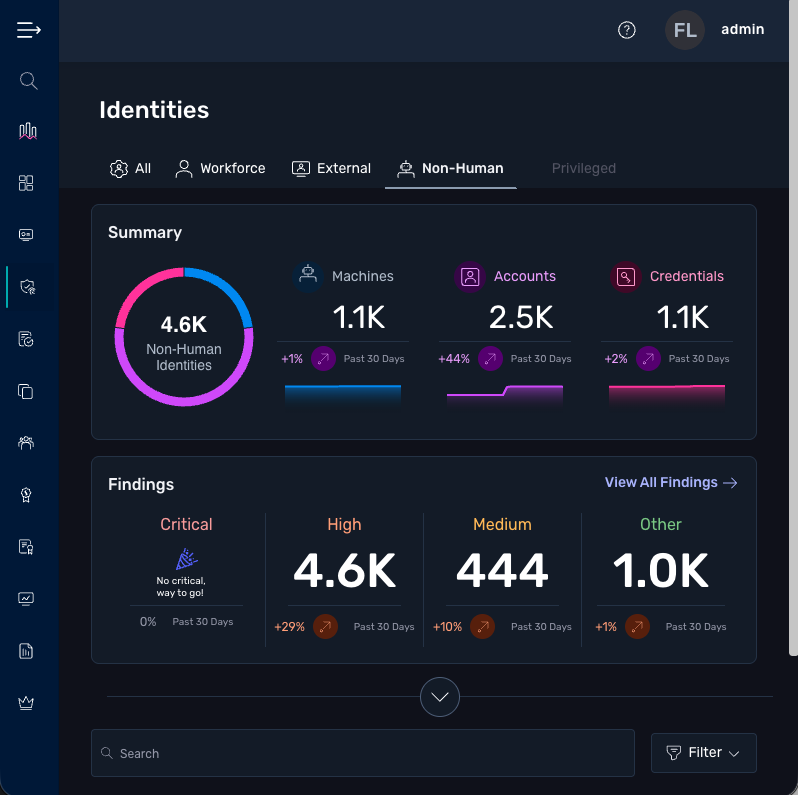
NHI dashboard
Automatically discover all workloads, accounts, and credentials across your environments.
Unified NHI policy view
Gain complete visibility into all NHI policies, including violations, status, and severity, in a unified view.
View personalization
Customize your view with flexible filters, sort by identity type, ownership, risk level, and more.
Identity-Centric Security: Leveraging AI for Scalable, Future-Ready Program
Learn how AI-powered identity security platforms can become the cornerstone of a scalable, resilient, and future-ready cybersecurity strategy.

Solutions for managing all identities — human or non-human
Elevate your security posture
Proactively detect access risks and ensure audit-readiness for both human and non-human identities.
.jpg?noresize&width=327&height=177&name=ISPM%20Main%20Dashboard%20Squared%20(2).jpg)
Real customers, real results
“Saviynt’s solution will significantly enhance our security, as we will know who has access to data and whether or not that access is appropriate.”
.jpg?noresize&width=2119&height=1415&name=iStock-1299972215%20copy%20(1).jpg)
“Our legacy platform was manual, labor-intensive, and a burden to maintain. Saviynt supported our move to the cloud and delivered a single, centralized identity and access platform for serving all 12 of our brands.”
Resources for your NHI security journey
Recognized market leader by top analysts
Saviynt Named a Gartner® Magic Quadrant™ for Privileged Access Management

Saviynt Named a Leader in KuppingerCole’s Identity Fabrics Leadership Compass Report

Saviynt Named a Leader in Frost Radar™ Report for Non-Human Identity 2025
Frequently Asked Questions
Non-human identities (NHI) are digital identities used to represent software workloads, robotic process automation (RPA), and other non-human actors within IT environments. They are not limited to machine identities — a common misconception — and include a broader range of identity types that interact with systems, data, and applications.
Key Components of Non-Human Identities:
- Machines and Workloads: Entities that perform actions
- Workloads – VMs, containers, serverless functions
- Bots – RPA bots, scripts
- AI Agents – Autonomous or semi-autonomous digital agents
- Devices – Physical devices like IoT sensors, smart cars, medical devices
- Accounts: Unique identity representations within specific systems or applications
- IAM roles, service accounts, system accounts, service principals
- Credentials: Secrets used to authenticate and authorize access:
- Tokens, certificates, API keys, SSH keys
As enterprises increasingly adopt automation and AI agents, non-human identities security has become a critical extension of identity security and cloud entitlement management. Non-human identities already outnumber human users, and the gap is widening.
Without proper oversight, these non-human identities become a major blind spot in the security landscape. Non-human identity security is critical to reduce the attack surface, prevent misuse of credentials, and maintain compliance—just as it is for human identities. A unified, governance-driven approach ensures that all identities are visible, controlled, and protected.
To effectively secure non-human identities (NHI), the first and most critical step is to establish comprehensive visibility across your environment. This means identifying all non-human actors along with their associated accounts, credentials, and access relationships.
Beyond basic inventory, it’s essential to gain contextual insights into their access, ownership, and lifecycle events. A timeline-based view that captures key activities—like ownership changes, and permission modifications—paired with risk-level classification, allows security teams to not only understand how these identities operate but also to prioritize remediation efforts.
Starting with visibility ensures a strong basis for governance and continuous compliance across all identity types.






%20(1).webp?noresize)
-1.png?noresize)