Key Strategies To Address Cybersecurity Gaps Caused by the Ever-Expanding Threat Landscape in the Healthcare Sector.
Healthcare will always be a top target for cyberattacks due to the nature of the information health systems work with and store. Over the past few years, the rapid march to cloud adoption, the proliferation of IoT technologies, and the rise in the use of contractors and other third parties, have dramatically expanded and reshaped the identity threat landscape, not only increasing challenges for security administrators but for front line and back office staff as well. While statistics by HIPAA Journal show a decrease in the number of unauthorized/disclosure incidents reported in 2022 (113 down from 130 in 2021), the number of records compromised in such incidents increased to more than 7 million in 2022 after a decrease between 2020 and 2021.
Unfortunately, due to the historical and distributed nature of technology adoption within the healthcare sector, security programs often become a patchwork of controls, management systems, and user interfaces. This results in blind spots in security and increased costs associated with licensing fees, training, and lost productivity.
Worse, the combination of fragmented security architectures with the difficulties staff can have getting proper access to the data they need can hinder patient care.
In this four-part blog series, we’ll touch on four key areas where converged identity platforms support positive patient and business outcomes. They are:
- Empower the Workforce
- Improve Operational Efficiency
- Protect Patients, the Workforce, and the Organization
- Enable Compliance
Read on to learn about how converged identity platforms allow you to increase efficiency and security by empowering your workforce.
How Converged Identity Platforms Allow You to Empower Your Workforce
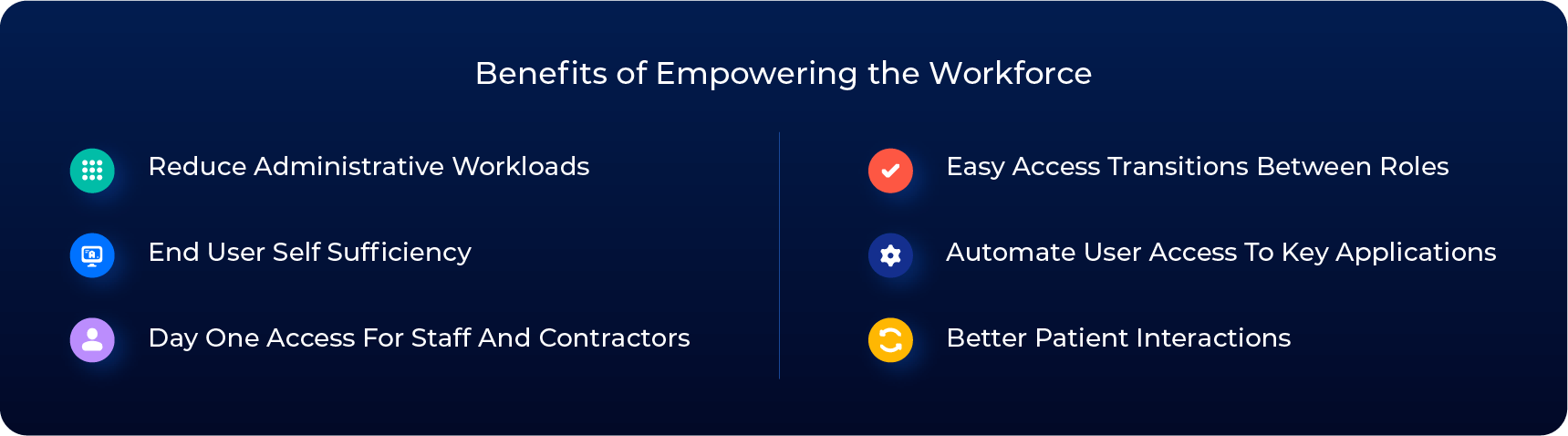
By unifying identity security into a single platform, healthcare providers can empower their workforce and enhance security programs. Empowering the workforce through a converged identity platform facilitates timely and appropriate access with minimal friction. It also provides self-sufficiency through intuitive and user-friendly tools and processes to alleviate administrative burdens. These capabilities allow staff to quickly access the information they need to deliver timely and appropriate services.
Streamline and Automate Access Requests
Deliver frictionless access by meeting staff where they are and using their preferred form of communication: mobile apps, integration with Microsoft Teams or Slack, or using an ITSM system such as ServiceNow. Providing users with a consistent method for access requests prevents them from having to learn different processes and programs to access needed applications and data.
Leveraging rule-based auto provisioning allows employees to quickly gain access to the information they need, including day-one access, to reduce productivity losses. Additionally, converged platforms let you link to other programs, such as your learning management system, to grant access immediately upon completing training in support of regulatory compliance.
Manage Privileged Access
There are numerous instances when privileged access is required within a healthcare organization. The trick is to limit this access as much as possible. For example, Saviynt Healthcare Identity Cloud’s (HIC’s) Just-In-Time access elevation capabilities let organizations reduce the threat landscape by restricting when and how long someone’s elevated privileges last.
Easily creating, approving, and monitoring time-bound access provides users with the elevated access they need when needed and for the proper length of time. Additionally, approval for requests can be automated based on specific risk factors.
Include Third Parties
Currently, up to 50% of a healthcare provider’s staff may be contracted out to third parties. Not often traditionally overseen by security teams, managing third parties has never been easy. As healthcare providers have continued to shift towards using an increasing number of individual contractors, visiting staff, and suppliers, third-party identity governance has become a critical component in reducing the threat landscape and maintaining regulatory compliance.
Converged platforms deliver third-party management with the ability to provide self-service registration for the onboarding of non-employees while also streamlining the requesting of access to clinical applications, regardless of identity type. They also help ensure governance is handled by the IT or security teams, not by HR or individual business units.
A Converged Identity Platform Designed for Healthcare Organizations
Saviynt Healthcare Identity Cloud (HIC) helps alleviate the challenges associated with effective identity security management and delivery to ensure healthcare providers can focus on their primary mission, providing outstanding patient outcomes. Saviynt HIC converges Identity Governance and Administration (IGA), Privileged Access Management (PAM), Application Access Governance (AAG/GRC), and Third-Party Access Governance (TPAG) onto a single platform that centralizes critical identity security program components.
Ensuring efficient patient care means staff, whether internal or external, are able to quickly access information. Converging identity access capabilities onto a single platform streamlines access and ensures efficiency by making sure employees are empowered by reducing friction. In our next post, we’ll focus on how converged identity platforms improve operational efficiency for healthcare providers.








.png)
