The Number of Third-Party Identities in Healthcare has Grown Dramatically in Recent Years. Here’s How to Handle the Increased Complexity They Bring.
The healthcare environment has changed dramatically since HIPAA was enacted in 1996. Digital transformation has affected changes in daily operations. Electronic Health Record (EHR) platforms are now an integral part of everyday life. Securing electronic access to tools and protected health information (PHI) has become critical to patient care, research, and business activities.
But this is not an easy prospect. The number of external identities has increased dramatically as healthcare organizations rely more on external resources. It’s not uncommon to see 25% or more of the identities within a healthcare organization originating from third parties such as vendors, medical schools, and outside hospitals and clinics.
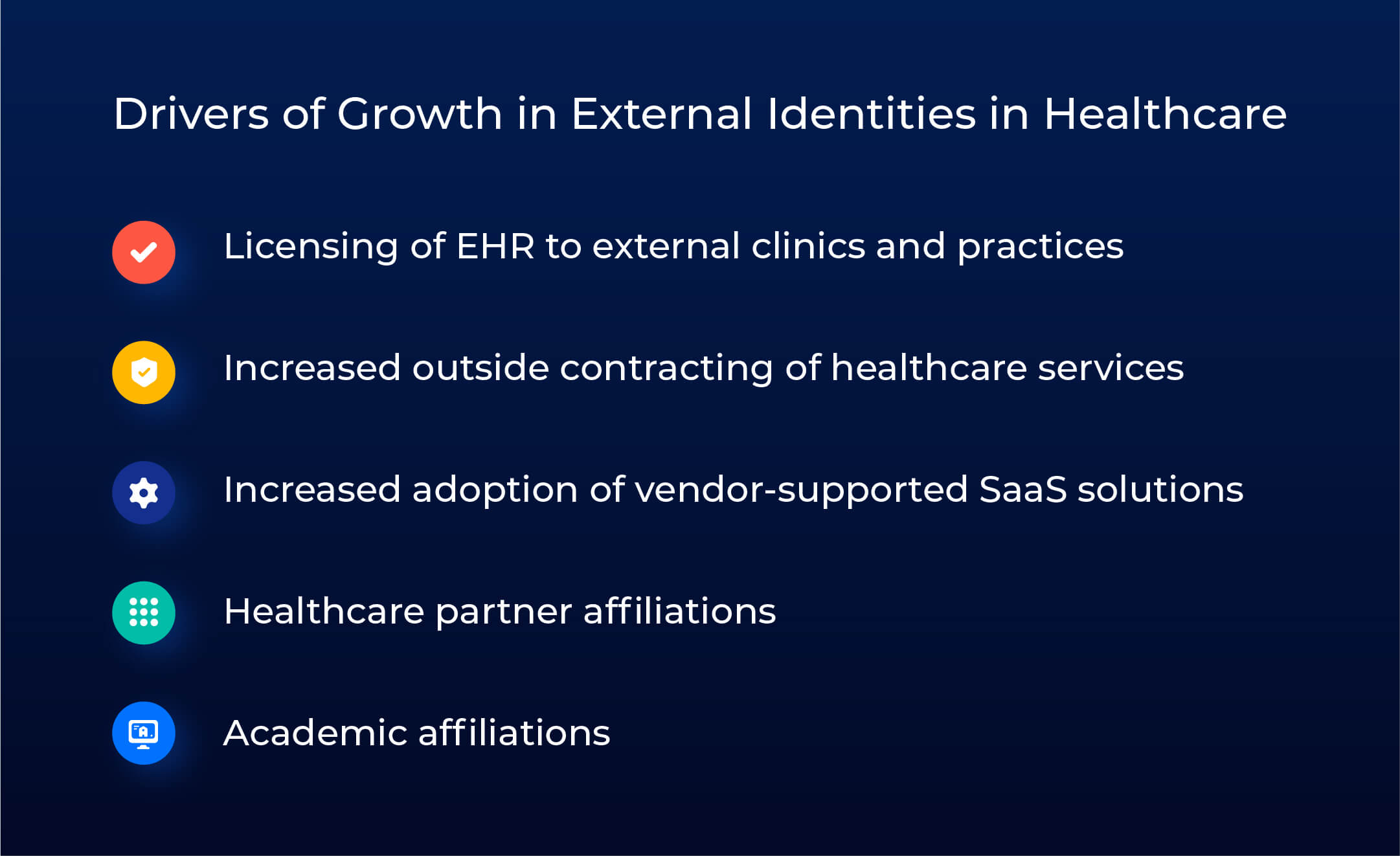
Where Did All These Identities Come From?
It’s becoming standard practice for hospital systems to contract with outside physician groups, laboratories, billing firms, analytics providers, and vendor-supported software solutions. Mergers and acquisitions have also impacted the identity space, with organizations needing to quickly and securely merge large numbers of identities into their existing environments. Teaching hospitals also need to maintain access for faculty and students at multiple academic institutions.
Additionally, large hospital systems have begun outsourcing their EHR resources to smaller providers, delivering siloed access within their own instances, essentially becoming SaaS providers to other organizations, and increasing the number of outsiders needing access.
The result of all this growth? Healthcare organizations struggle with complex and fragmented identity environments that fail to deliver the same level of services or security controls for external identities as they do for internal staff. The result is poor service levels and increased risk exposure.
Workaround Solutions to Third-Party Identities Increase Complexity
Most healthcare organizations have not had the luxury to execute a strategic approach to governing third-party identities. More typically, organizations have been put in difficult situations where they have had to act quicky and implement something to solve an immediate access need for third parties. These workarounds often include manual “back door” entry of identities by admins, or placing the burden on HR to process these users through the HRMS system, which is time consuming and an ineffective use of HR resources and tools. The service levels for these workarounds tend to be slower and resource intensive, and there is often little to no ongoing governance of these identities once they are added to the environment.
Five Key Techniques for Managing Non-Employee Identities
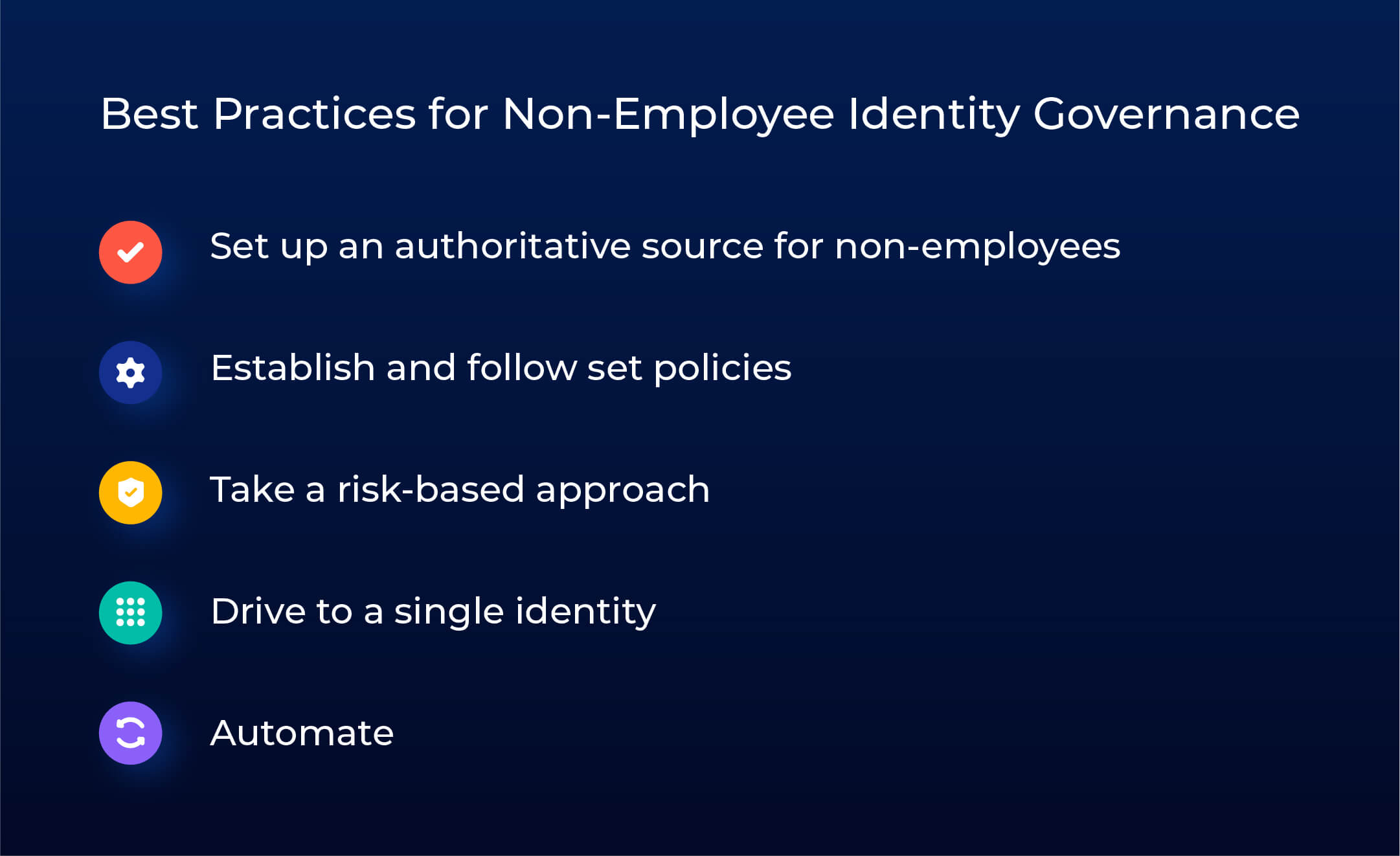
So, what’s an organization to do when governing external identities? Below are a few best practices organizations can use to help streamline governance and get control of external identities.
Delegate Administration to Your Trusted Third Parties
Consider giving trusted third parties the ability to administer and govern their identities directly in your environment. With the right agreements and technical guardrails in place, delegating administrative tasks to the vendor can:
- streamline the onboarding/off-boarding process,
- reduce access delays
- improve governance
To do this securely, you need to have policies in place and the ability to set technical controls to limit external administrators’ access to approved workflows.
Policy Establishment is Critical
You have the least control over the people you know the least about. And you know the least about external employees. While internal hires have well-defined processes, outside identities often aren’t subjected to the same stringent processes. Yet they have just as much, or potentially more, access to information and systems. Some of this is due to the nature of their jobs, but more often, it has to do with a lack of oversight, leading to overprovisioning of access.
Establishing well-defined processes for joiner, mover, and leaver activities not only provides continuity across the organization but also allows the ability to maintain continuous compliance and successfully complete audits. As a general rule, consider adding tighter birthright rules with access expiration dates and perform certifications more often.
Take a Risk-Based Approach
Vendors should have different access to information based on the nature of the work they do for the organization. By classifying the risk they pose to the organization, you can better establish the type access they have and the scrutiny their employees go through. The higher the risk associated with a relationship, the tighter the control needed.
Make sure to include vendors as part of your GRC program. Classify them based on the risk posed by the service they provide. Be sure to restrict access to highly sensitive systems and resources. Doing so helps establish timely revocation of access for their employees or the vendor itself, as appropriate or as the relationship changes.
Drive to a Single Identity
More sources of identity = more potential duplicates. When external identities are “back doored” into an environment through manual entry, identity matching is often bypassed or rendered ineffective due to lack of identifying data being captured. To mitigate this, establish third-party onboarding processes that:
- enforce a mandatory minimum baseline of identifying data for every human identity being created in your environment
- run all new external identities through an identity matching algorithm, checking against all internal and external identities in your environment
Being able to prevent duplicates and trace access and activity to a single identity not only increases security, but also helps ensure patient privacy and allows for better auditing and compliance capabilities to meet regulatory requirements.
Automate Whenever and Wherever Possible
IT and security teams have long seen the benefits of automating processes when and where they can. There certainly may be circumstances where automation with an external organization is not possible or worthwhile. But for long-term partnerships with high volumes of churn, automation is the way to go. When automation is an option, use it! Automation serves several benefits, not only for administrators, but for end users as well.
For administrators, it ensures consistency, removes human error, and alleviates tedious, manual and time-consuming processes, similar to the example I provided earlier. End users benefit from a consistent experience that simplifies their engagement through joiner, mover and leaver processes.
These best practices certainly don’t cover everything, as that could easily necessitate the writing of a trilogy, but they do provide key areas to address when developing or enhancing your approach to managing external identities.
Third-Party and Non-Employee Tools
If you’re looking to improve third-party access governance, there are a few considerations you may think about when deciding on a specific technology.
Four key areas are:
- Lifecycle Management
- Non-Employee User Onboarding
- Ongoing Governance
- Termination
Saviynt’s Healthcare Identity Cloud (HIC) provides dedicated features for non-employee and third-party access governance, in addition to IGA, privileged access management, application access governance, and data access governance.