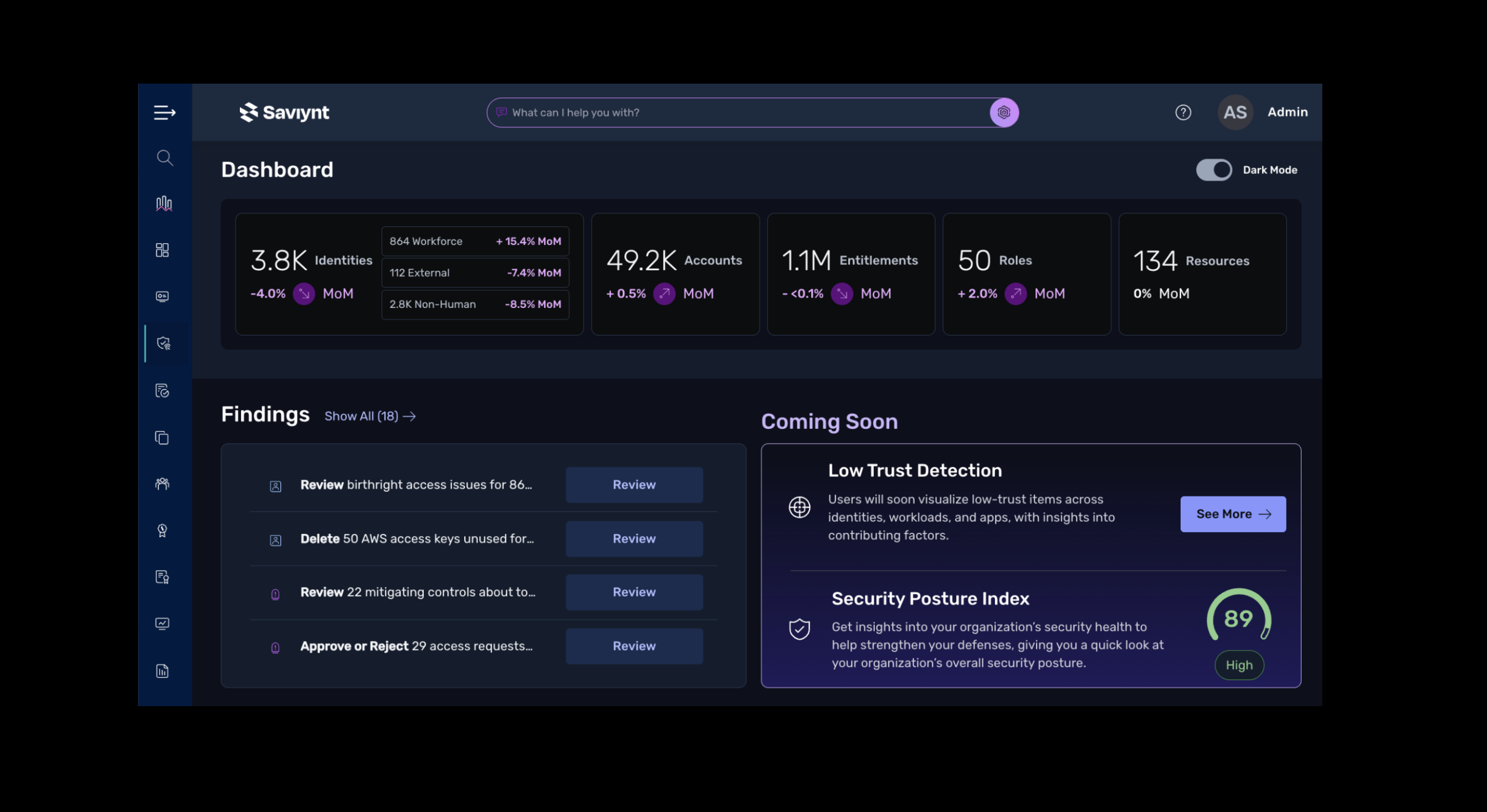
Powerful, Smart Identity Governance & Administration
Control risks for all identities and apps across your organization — without compromising productivity.
Secure your enterprise without slowing the business
Enable security for all identities and resources
Reduce decision-makers’
workload
Automate up to 75% of access review decisions and focus approvers’ attention on the most critical areas to reduce review fatigue and rubberstamping.
Help approvers make the right
access decisions
Eliminate the guesswork and reduce decision times for access requests and reviews by up to 70% with AI-powered recommendations and guidance.
Unify all your identity governance policies and audit process
Bring together your identity data, security controls, and compliance processes into a single platform for more comprehensive policy enforcement and easier audit reporting.
Reduce cost and
complexity
Eliminate the redundancies and management overhead of disparate security products, while gaining unified visibility and consistent control across your entire environment.
Modernize your
architecture
Accelerate deployment with a cloud-native platform and a catalog of pre-built integrations, enabling consistent identity security and governance at any scale.
Get complete identity governance, administration, and control
See the full identity security picture
Achieve an enterprise-wide view of access risks, across all apps, all entitlements, for all identities.
All identity types
Support traditional internal workforce users, plus external users, non-human identities and AI agents.
All apps and resources
Integrate with and manage all types of apps, platforms and ecosystems, such as SaaS, hybrid, on-prem, IaaS, ERP/EMR, CRM, and HR.
Solution Guide: Saviynt Identity Governance & Administration
Learn about the foundation of The Saviynt Identity Platform by diving into our identity governance & administration solutions capabilities.

Transform identity security with agentic AI
Enable every employee to manage access confidently and securely — just by using natural language. SaviAI provides contextual understanding and intelligent guidance, so users can effortlessly navigate complex identity decisions. Gain real-time insights and recommendations to turn identity interactions into a seamless experience: reducing tickets, accelerating productivity, and delivering smarter outcomes across the organization.
Supercharge app onboarding with AI-driven intelligence and eliminate months of manual effort. SaviAI learns patterns, autonomously configures connections, and brings even the most complex apps online in mere hours. Gain faster time-to-value and dramatically lower integration costs with conversational onboarding, governance, and security. It’s the new standard for identity integration in the age of AI.
Bring autonomous intelligence to identity-driven security operations — detecting suspicious activity, correlating risk signals, and recommending the right response in seconds. SaviAI provides contextual insights, guides triage, and automates remediation to streamline investigations, contain threats faster, and stay ahead of identity attacks, resulting in faster detection, smarter responses, and a stronger security posture.
Deliver next-gen autonomy to identity administration and precisely execute tasks while prioritizing security and compliance. SaviAI intelligently manages configurations, entitlements, policies, and lifecycle changes, significantly reducing effort and errors. Streamline operations and enforce consistent governance with contextual awareness and built-in guardrails for smarter administration, stronger security, and dramatically improved efficiency.
Identity security for all enterprise applications











5x Gartner® Customers' Choice
The only vendor named a Customers' Choice five years running for Identity Governance and Administration


%20(1).png?width=1980&height=1660&name=Untitled%20(1980%20x%201660%20px)%20(1).png)
Empower your entire identity security program
Govern privileged access
Accelerate your Zero Trust journey and ensure even the highest-risk access for all identities — human, non-human, AI agents, internal, or external — is secure.
.png?noresize&width=327&height=177&name=Dicovery%20and%20control%20(5).png)
Results from our global customers

“When it comes to audit and compliance, we could prove the new solution’s value from day one. Access terminations are pretty much immediate now. But here at Ingredion, we always aim to go above and beyond the bare minimum that’s required for compliance. We also saw productivity gains right away, because now new hires get access to resources from their first day on the job.”

“Our on-prem solution could only manage other things on-prem, and Saviynt has the ability to manage things both on-prem and in the cloud, so that was one of the things that made us realize that this is really a good solution for us in both realms.”

“Efficient onboarding helps our Petco partners (employees) hit the ground running, which in turn provides our customers and their pets with the best possible experience. We quickly found Saviynt to be a solution-oriented and customer-focused partner that supports our innovation."
.jpg?noresize&width=1359&height=800&name=banner-background-healthcare%20(1).jpg)
“None of us expected the level of visibility that Saviynt provided. It lifted the curtain. We’ve been able to collapse entire on-prem domains based on usage modeling of accounts and entitlements within those directories.”
Build a stronger identity security program
A recognized leader in identity governance and administration
Saviynt Named a 5x Gartner Customers’ Choice for IGA

Saviynt IGA Recognized as Industry-Leading by KuppingerCole

Saviynt Named a Leader in KuppingerCole’s 2025 Identity Fabrics Leadership Compass
Frequently Asked Questions
Identity Governance and Administration (IGA) is crucial for managing digital identities and access privileges within an organization. Its primary goal is to provide employees with seamless access to necessary data while simultaneously protecting that data from cyber threats and accidental disclosure.
IGA solutions also help companies maintain compliance with regulatory requirements. To achieve these objectives, IGA employs various interconnected tools, policies, and methodologies. These encompass several key areas, including identity management, data governance, and role-based access control policies, all while ensuring that IGA processes do not hinder operational efficiency.
The primary functions of an IGA solution are:
- Identity Lifecycle Management: This involves onboarding new users, creating accounts, granting and revoking access privileges, and continuously reviewing user access to ensure its ongoing relevance.
- Access Request Management: IGA software streamlines the process of requesting access privileges, making it a seamless, self-service experience that reduces the administrative burden.
- Access Control Policies: IGA solutions implement access control policies, such as role-based, resource-based, or attribute-based approaches, to grant access based on a person's role, authority, and security clearance.
- Policy Management: This crucial function allows the administration team to detect high-risk requests, enforce access policies, and prevent unauthorized system breaches.
- Auditing and Reporting: A strong IGA platform, like Saviynt's, includes auditing and reporting workflows to provide continuous compliance documentation, enabling management to trace the source of data breaches.
An IGA platform's primary benefit is enhanced security. It helps reduce data breaches and accidental leaks by limiting data access to only job-specific activities. Should a breach occur, an IGA platform minimizes damage by restricting the information an attacker can access.
Another key advantage of an IGA platform is its ability to ensure compliance with government and industry regulations. For example, in Europe, an IGA solution is crucial for adhering to the General Data Protection Regulation (GDPR), which not only safeguards data but also prevents hefty fines and public scrutiny.
Furthermore, an automated IGA approach boosts organizational efficiency. It frees up staff from manual tasks, such as granting or updating access privileges, allowing employees to focus on more productive work.
Modern, cloud-based IGA solutions also offer cost savings through machine learning. Beyond the management savings from automation, they eliminate the need to hire expensive professional services for customization or maintenance, and they reduce the risk of significant non-compliance fines.
Yes, an IGA platform can be highly effective when integrated with other security solutions. For instance, it can be combined with Identity and Access Management (IAM) solutions to verify that the correct individual is logging into their account. Additionally, it can connect with Security Information and Event Management (SIEM) software for continuous monitoring.
.png?noresize&width=336&height=336&name=PAM%20Webinar%20Feb%202026%201200x628%20Opt%203%20(15).png)




-1.png?noresize)
