IGA Modernization – Why Legacy Systems are Unsecure

By moving to the cloud, enterprises ease workload burdens, connect across Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS) and Software-as-a-Service (SaaS) to enable business operations. In a modern world where customers and employees increasingly access the cloud, organizations can no longer solely maintain on-premises IT infrastructures. Faced with legacy challenges, organizations seek to find the right approach for their cloud migration and hybrid architecture strategies. Unfortunately, despite wanting a modern modernize IT infrastructure that enables customers and employees, enterprises often forget that IT modernization needs to start with people which requires identity governance and administration (IGA) modernization as well.
What Are the Financial Benefits of IT Modernization?
Digital business models and digital operating models increase revenue by enabling new customer engagement models that drive growth.
The World Economic Forum highlights several benefits:
- 30% (estimated) of industry revenues will come from new models by 2020.
- 90% of companies adjusted their operations in the last two years.
- 26% more profit can be earned by companies that understand the digital transformation.
What Problem Does The IT Modernization Strategy Solve?
As a buzzword, digital transformation says very little. As a strategy, it says a lot because it enables the new customer engagement models that keep businesses relevant and drive growth. Modernization requires organizations to place technology at the core of their operations. It means looking at business objectives and creating a long term plan for growing revenue.
Thus, the questions that the enterprise must ask are:
- What are the corporate goals? These can be customer engagement or employee enablement, but the strategy needs to start with the purpose rather than the technology.
- What application tools can best meet these goals? Creating a multistage program and prioritizing deployment streamlines the transition.
- Who are the users? Business-critical operational goals define the strategy, but users (employees, customers, partners) need to define the deployment process.
IT modernization requires understanding the who, what, when, why, and how of cloud migrations. Creating a strategy that moves from a reliance on legacy infrastructures to cloud or hybrid infrastructures requires incorporating applications that not only answer these questions at deployment but provide visibility throughout the modernization life cycle.
WHAT ARE THE ACCESS SECURITY RISKS ARISING FROM IT MODERNIZATION?
Legacy IT infrastructures fail at securing data as organizations modernize their infrastructures. As data breaches increase in severity and numbers, organizations need to secure their mission-critical systems, networks, software, and applications. If one or more of the following describes your infrastructure, you likely have security vulnerabilities:
- Operating modern IT infrastructures in legacy environments increases complexity.
- Legacy IT infrastructures connected to the cloud create more entry points.
- Disconnected services across the ecosystem cannot be managed effectively.
- Fragmented identity systems create gaps that can lead to Segregation of Duties and “least privilege necessary” violations
With greater connectivity comes greater cybersecurity risk. Maintaining data integrity requires the enterprise to control data access and use. Legacy on-premises identity access management systems fail because they are unequipped for the increased connections that require additional internal and external users.
For example, SaaS platforms require access to cloud and data center resources. Not all users need the same access – some need privileged access, others limited, and some none. Since each SaaS vendor creates its own roles and access requirements, legacy IGA fails because it cannot aggregate the access management across the newly created ecosystem.
What Does IGA Modernization Mean?
IGA modernization means strengthening the web access management process. IGA modernization requires focusing less on the simple questions of “what and who” and focusing on the broader questions of “how and why.”
Legacy IGA Focus
Due to the static nature of on-premises IT infrastructures, IGA began with data then aligned it with users. Legacy IGA systems focused only on “who and what”:
- Create ID
- Set authentication
- Look up user access permissions
- Review the access control rule for role
- Compare individual’s access permissions to resource’s access control rules
- Grant if they match. Deny if they don’t.
The purpose of traditional IT was to provide information to people so they could do their jobs. This static IGA focus worked when organizations relied on internal, on-premises solutions.
Modernized IGA Focus
A modern access solution starts with people because cloud and hybrid environments exist to ease user pain points. People are not static. Digital business transformations focus on mobility to enable users. Remote employees connect to workplace IT infrastructures from laptops, tablets, smartphones, and smartwatches. Customers connect to digital engagement models in the same way.
To manage dynamic identities and access points, the enterprise needs an IGA solution that focuses on “when, how, and why” rather than simply “who and what.” IGA modernization requires solutions that focus on:
- Digital identity: human user
- Account: application the human user logs into and how much access they need
- Permissions: access right to a system focusing on system criticality to role
- Role: business role which often bundles with job function and establishes user criticality
- Policy: rules defining how a role or permission links to the identity or account
- Context: when and where the user logs in
- Attribute: a full aggregation of identity, account, permissions, role, and policy within a given context to create a holistic approach to identity and access
IGA modernization focuses less on the information and more on the way in which users need to access and interact with the information. However, focusing on people first means that IGA for digital business operations needs to be flexible and dynamic, just like the people using it.
Traditional digital identities focus on humans, but the increased use of applications and the cloud significantly change these definitions. Human users access applications, but also interconnected applications and devices accessing one another.
For example, an IaaS cloud such as AWS, Azure, or Google Cloud Platform, integrates with the connected SaaS applications, such as Office 365 or Dropbox. Therefore, these applications also need to be considered “digital identities” and managed that way the organization manages human identities.
Modernized IGA allows large enterprise users to define these electronic and human identities and give them specific access to cloud, on-premises, and hybrid IT environments so that organizations can manage all access to data. With greater visibility into these dynamic data interactions, organizations can prove governance over data access and refrain from SOD violations.
Why Digital Transformation Requires IGA Transformation
Legacy IGA solutions act as a paper map. They show routes and destinations. A person can follow a set pattern of roads to get where they need to go. However, a map created in 2000 is static, leaving out new infrastructures like new roads. Moreover, traffic changes by the minute.
Digital IGA solutions act like crowd-sourced GPS applications. Drivers adopting digital transformation use smartphones to plan their routes. These applications incorporate infrastructure changes so that drivers know what roads to access. Additionally, these applications provide real-time insight into new traffic patterns and provide alternative routes giving drivers visibility into their travel time.
IGA modernization enables businesses in the same way as GPS applications. As organizations migrate to the cloud, they need solutions that match dynamic user access. They need near real-time visibility into infrastructure changes, such as new applications added to the IaaS or PaaS environment. They need to know when people access systems, software, and networks to ensure appropriate use. They need to know where people access their ecosystems to gain insight into whether that access is appropriate.
How Saviynt Accelerates Digital Transformation with IGA Modernization
Saviynt starts with people. Our IGA solution enables cloud, hybrid, and on-premises IT infrastructures that start in the cloud and enable full visibility into how and where users interact with data.
As a SaaS platform, we understand that we are another third-party vendor whose risk our customers need to manage. As the first and only Identity Access Management provider to achieve FedRAMP ATO status, we accelerate customer cloud migration strategies by providing them assurance over our information security controls, easing the vendor risk management process.
Starting with people, Saviynt provides an intuitive user experience because ease leads to adoption.
The Identity Governance Access (IGA) module allows organizations to compare user access behavior to peers to accelerate cloud migration. By comparing a user’s behavior to their peers, the enterprise has insight into whether the user access request is similar to others or different, thus lowering the risk of elevated access, maintaining “least privilege necessary” policies, and reducing Segregation of Duty (SOD) violations.
With the Cloud Privileged Access Management (PAM) module, an enterprise can monitor privileged users to ensure that they do not abuse their rights while also providing time-bound escalations to mitigate potential access violations. Moreover, our cloud-native capabilities and integrations accelerate IT modernization by providing visibility into the interconnected ecosystem.
The risk-based Data Access Governance (DAG) allows an enterprise to classify data, protect data in real time, review access analytics, and ensure compliance with internal controls.
With compliance rapidly acting as a barrier to cloud migration, Saviynt eases the burden by incorporating native integrations with common IaaS, PaaS, and SaaS services such as AWS, Azure, Oracle, Google Cloud Platform, SAP HANA, GitHub, Chef, Puppet, SAP, Office 365, Box, SharePoint, Dropbox, WorkDay, SalesForce, and Google Apps. The Saviynt platform also offers a controls library incorporating suggestions for the most common application and compliance requirements including HIPAA, HiTRUST, SOX, PCI DSS, CPPA, GDPR, ISO 2000 series, and NIST.
To learn more about how Saviynt’s modern IGA solution eases the risks associated with modernizations, read our whitepaper “Identity Governance and Administration: Enabling Digital Transformation with Identity 3.0.”
Related Post
03 / 11 / 2026
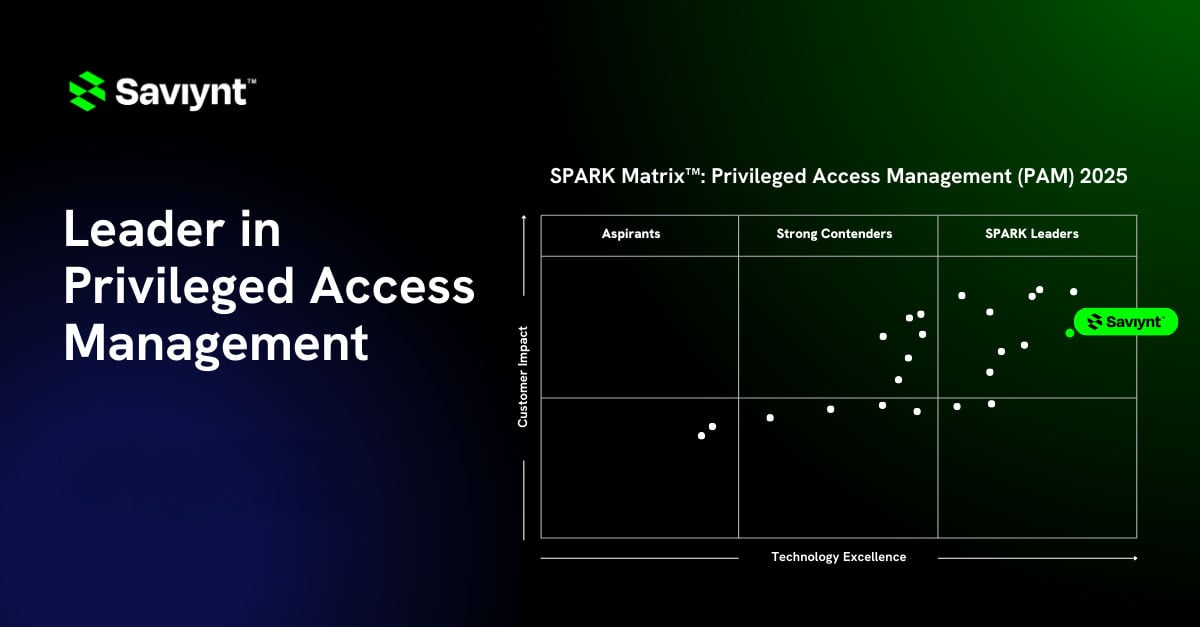
Saviynt Named a Leader in SPARK Matrix™: Privileged Access Management (PAM), Q4 2025
READ BLOG


Report
Saviynt Named Gartner Voice of the Customer for IGA

EBook
Welcoming the Age of Intelligent Identity Security

Press Release
AWS Signs Strategic Collaboration Agreement With Saviynt to Advance AI-Driven Identity Security

Solution Guide