Content Hub
Research, Advice, and Best Practices From Identity Experts
Content Type
Content Type
- All Content Type
- EBook
- Analyst Report
- Whitepaper
- Data Sheet
- Case Study
- Solution Guide
- On-Demand Webinars
- Video
- Article
- get solution
Industry
All Industry
- All Industry
- Energy
- Federal Government
- Financial Services
- Healthcare
- Higher Education
- Manufacturing
- State & Local Government
- Retail
Solutions
All Solutions
- All Solutions
- Application Access Governance
- The Identity Cloud
- Identity Governance & Administration
- Privileged Access Management
- External Identities & Risk Management

On-Demand Webinars
From Siloed SAP to Centralized Enterprise Governance: A Practical Playbook





.jpg)

Analyst Report
Saviynt named a Leader in KuppingerCole’s 2025 Identity Fabrics Leadership Compass


On-Demand Webinars
GE Healthcare’s Journey to Proactive Identity Security with Identity Security Posture Management (ISPM)






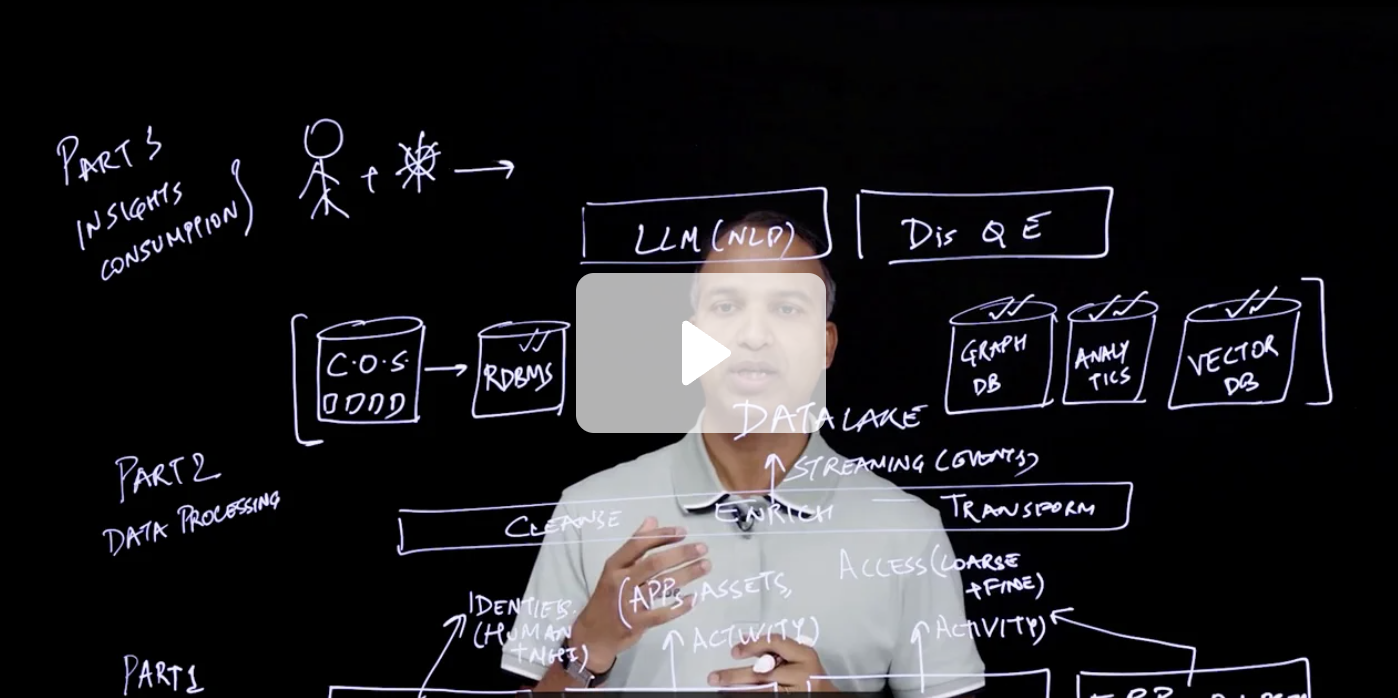
Video
Chalk Talk: The Science Behind Saviynt’s Identity Security Posture Management (ISPM)



Case Study
The University of Western Australia Finds Power and Simplicity in the Cloud
Analyst Report
Saviynt Named a Customers’ Choice in the Gartner® Peer Insights™ Voice of the Customer for IGA Report

On-Demand Webinars
Innovative IAM Strategies: New Tools and Guidance for Modern Identity Security

On-Demand Webinars
From Fragmented to Unified: Transforming IAM in the Age of Digital Complexity
.jpg)
On-Demand Webinars
Powering and Protecting the Extended Workforce with an Identity-Centric Approach
.jpg)
Analyst Report
Saviynt named a Leader in KuppingerCole’s 2024 Identity and Access Governance Compass Report

On-Demand Webinars
Transforming Access Management: Strategies for the New Digital Landscape

On-Demand Webinars
Unlocking the Promise of Productivity in Your Third Party Workforce
Analyst Report
Saviynt PAM is Recognized as a Value Leader by Analyst Enterprise Management Associates (EMA)
.jpg)
On-Demand Webinars
Analyst Webinar | The Need for Identity Intelligence: How Identity Proliferation is Changing Identity Security

Analyst Report
Saviynt included in the 2024 Gartner® Market Guide for Identity Governance and Administration (IGA)



.jpg)
.jpg)
.jpg)
Analyst Report
Saviynt Identity Cloud IGA Capabilities Recognized as Industry-Leading by KuppingerCole Analysts AG

On-Demand Webinars
How Unified IGA and PAM Can Protect Organizations from Ransomware and Other Identity-Based Threats

Video
Joiners, Movers, Leavers, and Failures: Why is Identity Management Still Struggling?
.png)




On-Demand Webinars
Navigating Identity Governance in Financial Services: Navy Federal Credit Union's Journey with Saviynt & Accenture



Case Study
Ingredion Replaces Legacy Solution with Flexible, Modern Cloud IGA Platform



.png)
.png)
.png)




Case Study
Syneos Health Futureproofs Identity Governance for Flexibility and Rapid Growth












Analyst Report
Recognized By KuppingerCole Analysts As Leaders In The Access Control Market For SAP & Multi-Vendor LoB

Analyst Report
Recognized By KuppingerCole Analysts As Leaders In The Access Control Market For SAP
Analyst Report
Saviynt Cloud PAM is Recognized as Best Privileged Access Governance and Strong Value by Analyst Enterprise Management Associates® (EMA)
Analyst Report
Saviynt is named a Customers’ Choice in the 2023 Gartner® Peer Insights™ Voice of the Customer: IGA



-1.png)












On-Demand Webinars
Identity, Credentialing, and Access Management (ICAM) and Executive Order 14028




On-Demand Webinars
Use Identity Convergence to Collaborate More Securely with External Partners

On-Demand Webinars
Modern Identity Governance & Administration for Mid-sized Organizations
On-Demand Webinars
Identity Security Converged: Expert Insights from Top International Brands





.jpg)
Ready to see for yourself?
Request a personalized demo with a Saviynt identity expert