Secure Your External Workforce
and Third-Party Access
Simplify and accelerate secure access for external identities such as contractors, vendors, franchises, and temporary employees.
Enable smarter, safer access control for external identities and third parties
Easily get external users and partners onboard
Provide right-time, right-level access
Ensure third party, external users have only the access they need to do their job, for the right amount of time, right when they need it.
Ensure third party governance policies are followed
Delegate administration of external users
Make audits and compliance a breeze
Close out projects with confidence
Simplify and accelerate secure access for external identities

Find external users already in your system
Identify the external users already present in your organization and bring them under management to ensure visibility and security.
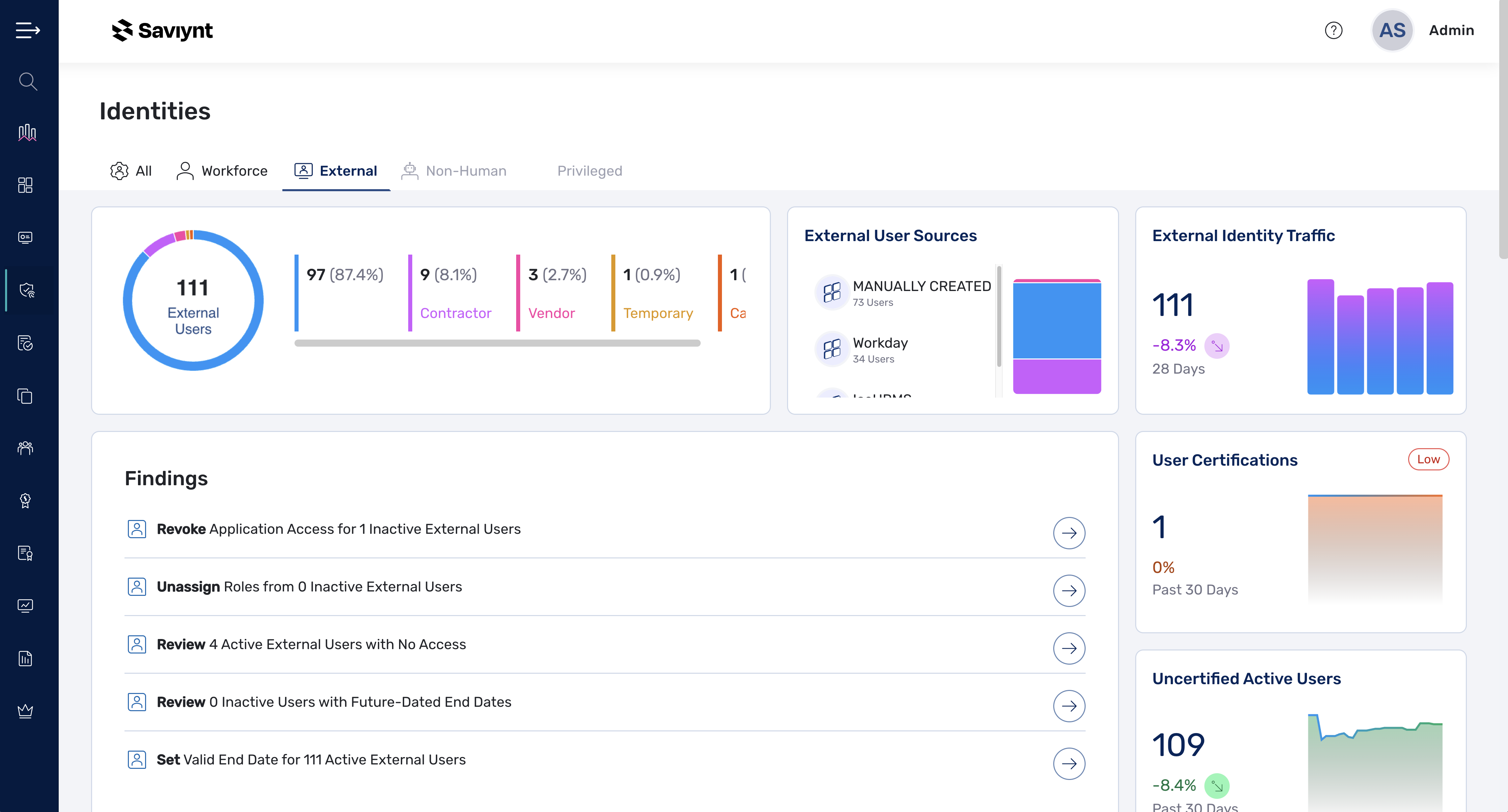
Listing of external users
Easily identify external users anywhere in your system with their current status and entitlements.
Classification rules
Organize existing external users to ensure they are included in roles, rules and analytics that apply.
.png?noresize&width=327&height=177&name=Inventory%20External%20Users%20(1).png)
Understand The Hidden Risks of Third-Party Access
How many vendors have the keys to your kingdom? Use this guide to inventory, onboard, and provision with confidence.

Empower your entire identity security program
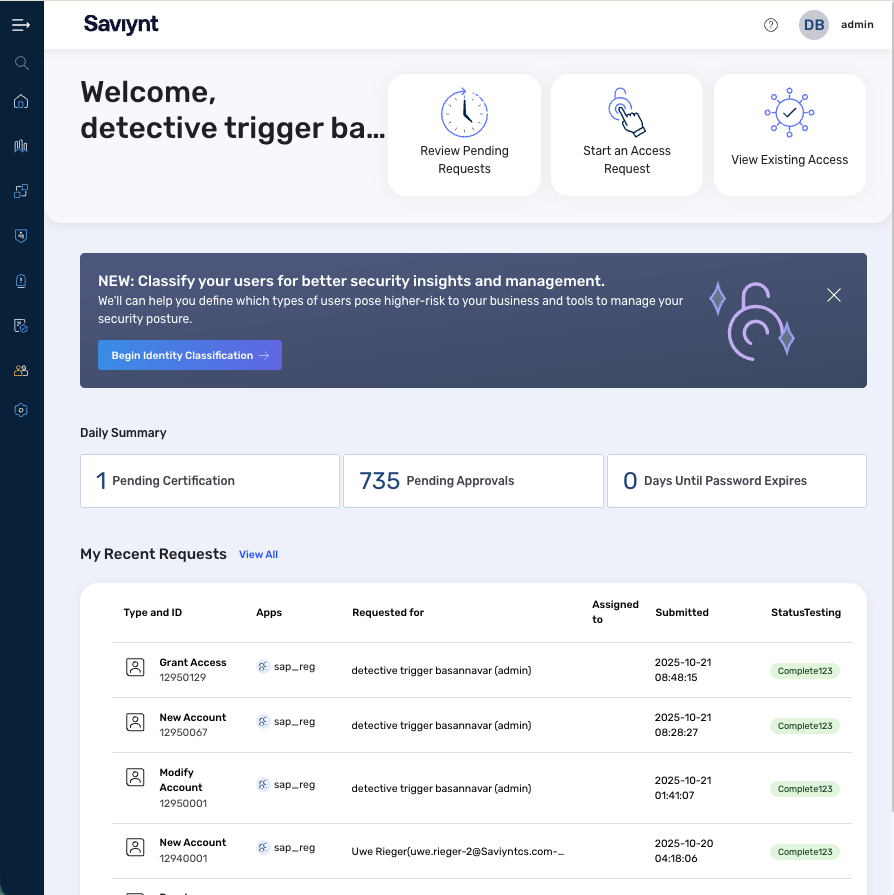
Boost security and efficiency
Enforce holistic identity security policies for internal and external users, across cloud, on-prem, and hybrid environments without straining your admins or users.
.png?noresize&width=327&height=177&name=IGA%20dashboard%20(4).png)
Real customers, real results
.jpg?noresize&width=2119&height=1415&name=iStock-1299972215%20copy%20(1).jpg)
“Our legacy platform was manual, labor intensive, and a burden to maintain. Saviynt supported our move to the cloud and delivered a single, centralized identity and access platform serving all 12 of our brands.”
.webp?noresize&width=1702&height=1174&name=uwa-bg%20(1).webp)
“Saviynt’s solution will significantly enhance our security, as we will know who has access to data and whether or not that access is appropriate."

-1.png?noresize&width=336&height=336&name=Untitled%20design%20(50)-1.png)
