Arrêter les risques de conformité et de sécurité des applications avant qu'ils ne commencent
Mettez en œuvre une gouvernance des apps pilotée par l'IA pour sécuriser les apps critiques, réduire les coûts de conformité et prévenir la fraude.
.png?noresize&width=1110&height=587&name=Untitled%20design%20(94).png)
Gouverner l'accès à chaque application avec intelligence et précision
Supervision unifiée de l'accès
Visibilité complète de l'application
Application granulaire de la politique
Contrôle des risques piloté par l'IA
Remédiation proactive à la fraude
Automatisation rentable de la mise en conformité
Éliminer de manière proactive les risques liés aux applications
.png?noresize&width=981&height=729&name=Untitled%20(435%20x%20363%20px).png)
.png?noresize&width=435&height=363&name=Untitled%20(435%20x%20363%20px).png)
Découvrir l'accès détaillé aux applications critiques
Obtenez des informations précises et en temps réel sur les accès et les droits pour des applications telles que SAP et Oracle à l'aide de tableaux de bord analytiques avancés.
Tableau de bord des accès aux applications
Découvrez et visualisez automatiquement les accès et les droits à l'échelle de votre écosystème d'applications pour une transparence totale.
Vue d'analyse des droits
Explorez les droits détaillés à l'aide de filtres personnalisables, triez par type d'application, niveau de risque, propriétaire, etc. pour obtenir des informations ciblées.
Interface de visualisation des risques
Visualisez et hiérarchisez les risques d'accès en temps réel, en analysant les violations potentielles à l'aide de tendances graphiques et de rapports prêts à être audités.
.png?noresize&width=327&height=177&name=AAG%20-%20Fine%20Grain%20Visibility%20-%20Entitlements%20-%20Square%20(1).png)
Détecter les violations d'accès grâce à des règles d'application prédéfinies
Identifier instantanément les violations de la SoD à l'aide de jeux de règles préconfigurés et spécifiques à l'application pour SAP, Workday et Oracle, afin de rationaliser l'application de la conformité.
Tableau de bord des règles SoD
Appliquez automatiquement des ensembles de règles SoD préconçus pour détecter les violations dans les applications, ce qui vous permet de visualiser instantanément l'état de la conformité.
Interface d'analyse des violations
Examinez et hiérarchisez les violations SoD à l'aide de filtres pour le type d'application, la gravité du risque et les rôles des utilisateurs, afin de permettre des vérifications rapides de la conformité.
Portail de configuration des jeux de règles
Personnalisez et déployez des règles SoD spécifiques aux applications pour Oracle et Salesforce, afin de garantir une mise en œuvre automatisée avec un minimum d'efforts de configuration.

Identifier et hiérarchiser les risques d'accès grâce à l'intelligence artificielle
Exploitez les analyses pilotées par l'IA pour détecter et hiérarchiser les risques d'accès à travers les applications, ce qui permet une prévention proactive des fraudes et des violations.
Tableau de bord de hiérarchisation des risques
Visualisez et hiérarchisez les risques d'accès en temps réel à l'aide d'analyses pilotées par l'IA sur l'ensemble des applications, afin d'assurer une surveillance proactive de la conformité.
Interface de détection des anomalies
Analysez les anomalies à l'aide de filtres alimentés par l'IA, en triant les risques par gravité et par type d'app pour prévenir les violations et les fraudes.
Portail de notation prédictive des risques
Générez des scores de risque prédictifs pour les demandes d'accès, permettant une prévention préemptive des violations de la SoD et de la fraude, avec des alertes automatisées.

Examiner et valider efficacement les droits
Automatisez les examens d'accès grâce à des flux de certification intelligents, garantissant la conformité d'applications telles que Salesforce avec un minimum d'efforts manuels.
Gestionnaire de campagne de certification
Lancez des campagnes de certification d'accès automatisées pour des applications telles que Salesforce, en rationalisant les examens des droits grâce à des flux de travail de conformité préconfigurés.
Tableau de bord d'examen des accès
Contrôlez et validez les droits d'accès aux applications en temps réel, à l'aide de tableaux de bord intuitifs, afin de garantir la conformité avec un minimum de charges administratives.
Interface de workflow d'approbation
Personnalisez et approuvez les certifications d'accès à l'aide de flux de travail basés sur les rôles, afin de garantir une validation rapide et conforme des droits dans les applications critiques.

Fournir un accès temporaire aux applications avec un contrôle en temps réel
Accordez un accès sécurisé et temporaire avec un contrôle et une révocation de session automatisés, protégeant ainsi les applications critiques contre les risques d'utilisation non autorisée.
Console d'accès d'urgence aux applications
Fournissez rapidement un accès temporaire pour les applications critiques telles que SAP, avec une surveillance automatisée pour garantir une utilisation sécurisée et conforme.
Tableau de bord de suivi des sessions
Surveillez les sessions d'accès d'urgence en temps réel, en visualisant l'activité des applications pour empêcher les accès non autorisés et garantir la conformité.
Workflow de révocation d'accès
Automatisez la révocation des accès temporaires à l'aide de flux de travail préconfigurés, sécurisant ainsi les applications telles qu'Oracle contre les abus et les risques d'audit.
.png?noresize&width=327&height=177&name=AAG%20-%20Emergency%20Access%20-%20Square%20(1).png)
Automatiser les audits tout en optimisant les coûts de licence
Rationalisez les audits et réduisez les coûts en automatisant la conformité et en identifiant les accès non utilisés dans les applications en nuage et sur site.
Portail d'audit de conformité
Automatisez les audits de conformité pour GDPR et SOX, en générant des rapports pour garantir le respect des réglementations avec un minimum d'efforts.
Tableau de bord d'optimisation des licences
Identifiez et éliminez les accès inutilisés aux applications pour optimiser les coûts de licence, en visualisant les économies réalisées sur SAP et Workday.
Workflow d'analyse des coûts
Analysez l'utilisation des accès à l'aide de flux de travail automatisés, réduisez les coûts de conformité et assurez une gouvernance efficace pour les applications critiques.
.png?noresize&width=327&height=177&name=AAG%20-%20Compliance%20and%20Cost%20Optimization%20-%20License%20Optimization%20-%20Square%20(1).png)
Rapport KuppingerCole : Saviynt Application Access Governance
Découvrez l'environnement des applications d'entreprise d'aujourd'hui et une analyse des capacités uniques et des avantages offerts par Saviynt.

Sécurisez votre entreprise grâce à une gouvernance intelligente de l'accès aux applications
Onboarding rapide pour chaque application
Éliminez les goulets d'étranglement généralement associés à l'intégration et à la gestion des applications en utilisant l'IA agentique pour intégrer rapidement n'importe quelle application, qu'elle soit connectée ou déconnectée.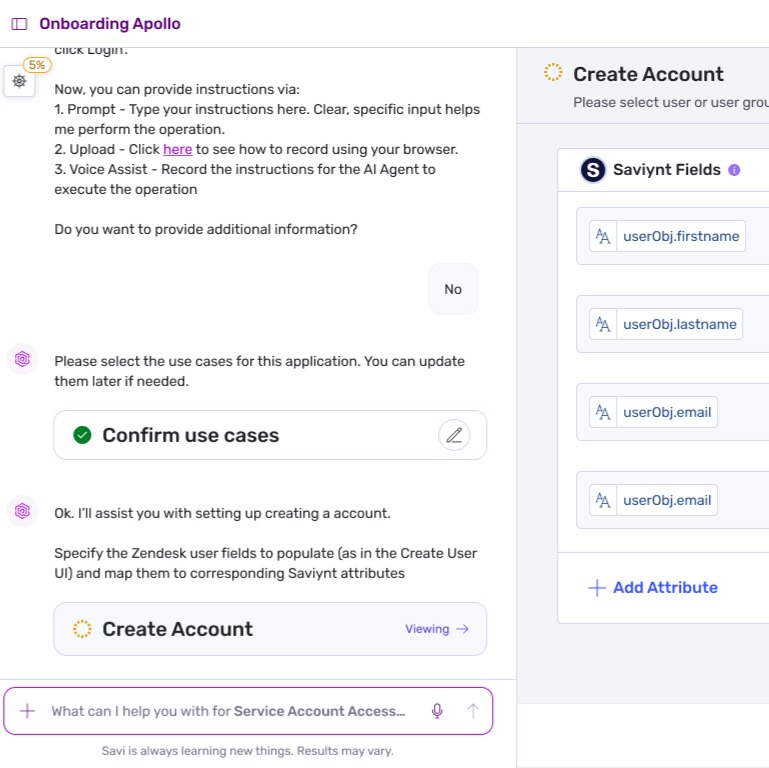
De vrais clients, de vrais résultats

"Dès le départ, Saviynt a fait preuve de flexibilité et de réactivité. Leur équipe n'a pas seulement été capable de répondre aux exigences uniques d'ADS, mais ils ont eu à cœur de le faire, en proposant des solutions qui ont rendu plus rapide et plus facile l'intégration des utilisateurs dans un environnement complexe comprenant un grand nombre de travailleurs saisonniers."

"Avant la mise en œuvre, nous nous appuyions sur des processus manuels et des outils d'automatisation localisés pour de nombreuses choses - l'intégration et la désinscription des employés, les attestations, les rapports et la création de contrôles d'audit. Désormais, nous disposons de processus automatisés d'attribution de comptes et d'accès, ainsi que d'une visibilité centralisée dans l'ensemble de l'entreprise. Nous pouvons voir qui a accès aux systèmes et aux ressources dans chaque région. L'amélioration de la visibilité et de la gouvernance a conduit à des améliorations significatives de la posture de sécurité globale de LIXIL.

"Avec Saviynt, nous avons pu atteindre une plus grande stabilité dans notre utilisation de l'automatisation. Nous avons automatisé le provisionnement des accès de droit de naissance et le processus de conversion des comptes dès que les rôles des personnes changent. Ce sont des choses que nous ne pouvions pas faire avec Okta.









