We're proud to share that Saviynt has been recognized as a technology leader in the QKS Group SPARK Matrix™: Privileged Access Management (PAM), Q4. To us, this distinction underscores that identity security and PAM are moving in the direction we've believed in for years. It has to live in the identity.
In this post, we'll break down what this recognition means, why privileged access management is changing, and how Saviynt is built for the privileged identities enterprises are managing today and the ones they'll be managing tomorrow.
Key Takeaways
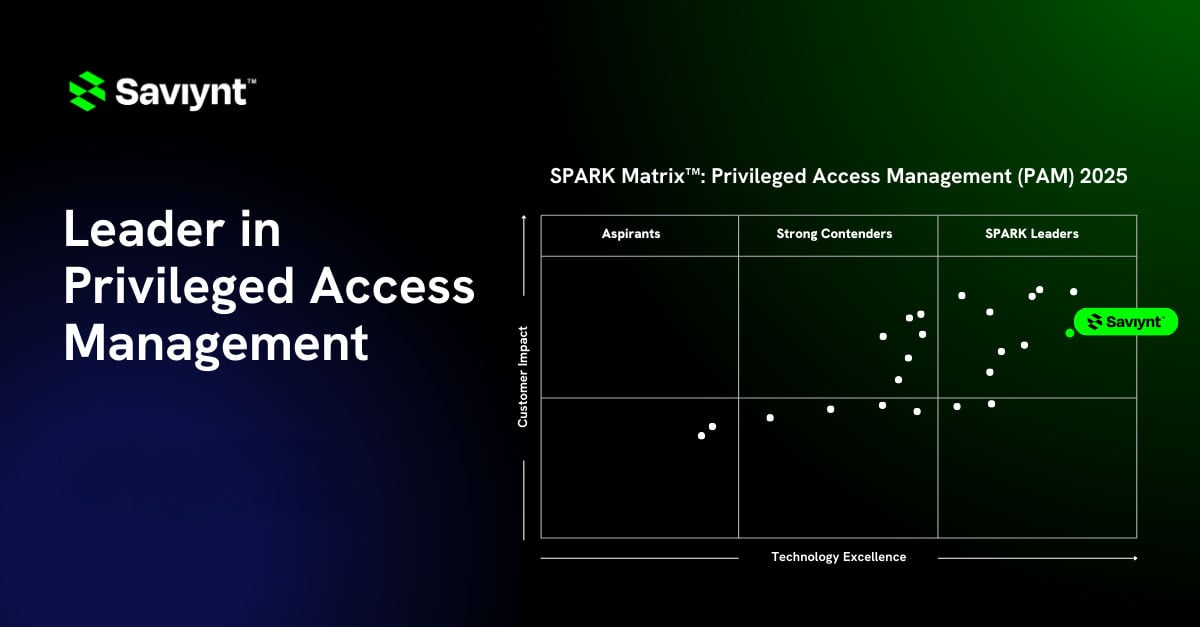
- Saviynt has been named a Leader in SPARK Matrix™: Privileged Access Management (PAM), Q4 2025, recognized for both technology excellence and customer impact.
- The recognition reflects Saviynt's unique convergence of PAM, Identity Governance and Administration (IGA), and Non-Human Identity (NHI) management into a single cloud-native platform.
- As AI agents and non-human identities proliferate across enterprise environments, traditional PAM is no longer sufficient. Saviynt is built for the future of identity security.
- Just-in-Time Access (JiT) helps organizations achieve Zero Standing Privilege, reducing the attack surface without sacrificing operational speed.
What Is the QKS SPARK Matrix™ for PAM?
The QKS SPARK Matrix™ is a global competitive evaluation framework used by security and IT leaders to benchmark technology vendors across two dimensions — technology excellence and customer impact.
In the context of privileged access management, the matrix measures how effectively a platform secures privileged identities while delivering real-world outcomes for the organizations that depend on it.
The PAM category is one of the most consequential in enterprise security. The 2025 Gartner® Magic Quadrant™ for Privileged Access Management described privileged access as access that "allows users to override existing access controls, modify security configurations, or make changes that affect multiple users or systems." The report noted that mismanaged privileged access "presents catastrophic risk." That framing hasn't changed, but the scope of who (and what) holds privileged access absolutely has.

The PAM Problem Has Changed. Has Your Solution?
There was a time when PAM meant locking down a small set of admin credentials in a vault. It involved a handful of IT administrators, a secret rotation, and a session recording tool. PAM was manageable and easily understood. That time has passed.
Today, non-human identities, service accounts, API keys, cloud workloads, bots, and AI agents vastly outnumber human ones in most enterprise environments. These identities don't clock in and out. They operate continuously, often with sweeping access to production systems, sensitive data, and critical infrastructure. And they're multiplying faster than traditional PAM tools were ever designed to handle.
Add to that the rapid expansion of AI agents. These autonomous systems are now provisioned with the kind of access that, a few years ago, would have been reserved only for senior engineers or system administrators. As Saviynt CEO and Founder Sachin Nayyar put it, "As emerging AI agents increasingly require privileged access, PAM is becoming mission-critical to securing the front lines of the enterprise."
Enterprises that are still relying on legacy, on-premises credential vaults to address this reality aren't just understaffed; they're structurally misaligned with the threat landscape they're facing.
How Saviynt Stands Out in the QKS SPARK Matrix™
Saviynt's recognition in the QKS SPARK Matrix™ reflects a fundamental architectural difference from legacy PAM providers. We built PAM inside an identity platform, not alongside one.
Where traditional tools treat privileged access as a separate layer to bolt on after governance is already deployed, Saviynt's Identity Cloud converges IGA, PAM, Application Access Governance (AAG), and Identity Security Posture Management (ISPM) into a unified platform. The result is a PAM experience that doesn't just lock down credentials, but continuously understands the risk context behind every access request.
Several core capabilities set Saviynt’s PAM solution apart from others:
- Agentless, Zero-Touch Architecture. Saviynt delivers secure privileged access without requiring heavyweight agents deployed across every endpoint. This means organizations can stand up modern PAM capabilities in days instead of months, and without the complexity and maintenance overhead that has made legacy deployments so painful.
- Just-in-Time Access and Zero Standing Privilege. Rather than granting permanent elevated access and hoping it isn't abused, Saviynt's model provisions access precisely when it's needed and revokes it the moment it isn't. This dramatically compresses the exposure window for any given privileged session and is one of the most effective architectural responses to insider threats and credential-based attacks.
- Unified Governance Across Human, Non-Human, and AI Identities. Saviynt extends PAM beyond human administrators to service accounts, API credentials, cloud workloads, and AI agents — bringing the same governance rigor to machine identities that enterprises have long applied to people. This matters enormously as organizations scale their AI deployments and find themselves managing privileged access for systems that operate autonomously.
- AI-Driven Risk Intelligence. The platform uses machine learning to continuously evaluate the risk profile of every identity and access request — surfacing anomalies, flagging misconfigurations, and triggering automated remediation before small exposure windows become large breaches.
- Cloud-Native and Multi-Cloud Ready. Saviynt's SaaS architecture is built for today's hybrid and multi-cloud realities, integrating natively with AWS, Azure, GCP, and the modern enterprise stack without the infrastructure burden of legacy vault-based solutions.
What Saviynt’s Position in the QKS SPARK Matrix Means for Security and Identity Leaders
For CISOs, IAM architects, and identity program managers evaluating the PAM market, this recognition from QKS provides an independent data point that Saviynt's approach is resonating both technically and operationally.
More importantly, it reflects a shift in what good PAM looks like in 2026 and beyond. The organizations best positioned to manage privileged risk aren't the ones with the most locked-down vaults. They're the ones who have built a living, adaptive governance layer that follows every identity wherever it goes, whatever form it takes.
Saviynt's position in the QKS SPARK Matrix™ reflects our vision for the future of Identity Security. And the $700M KKR-led investment we announced in December 2025, at a valuation of approximately $3 billion, signals that the market believes in our vision too.
Why Analyst Recognition for PAM Matters (and Why It Doesn't Tell the Whole Story)
Placements in frameworks like the QKS SPARK Matrix™ carry real weight when security and IT leaders are building their evaluation shortlists. They synthesize independent research across the vendor landscape and cut through marketing noise.
But the most meaningful validation comes from the organizations trusting Saviynt to protect their most critical assets. We protect Fortune 500 companies, global financial institutions, and government agencies where the cost of a privileged access breach isn't an abstract risk. It's a headline with real repercussions.
Recognition from QKS Group validates that what we're building maps to what enterprises actually need. Our customers validate that it works.
The Future of Privileged Access Management
The PAM market will keep evolving, and Saviynt will keep building. Our roadmap focuses on deepening AI-powered access decisioning, expanding our Non-Human Identity Management capabilities, and making Zero Standing Privilege achievable not just in theory but at enterprise scale and across the most complex, distributed environments in the world.
Privileged access isn't a solved problem. It's an ongoing discipline. And as AI agents proliferate and the definition of privileged continues to expand, the organizations that treat PAM as a strategic identity security investment — not a compliance checkbox — will be the ones that succeed.
We're honored to be recognized by QKS Group as a leader in that work.