Trust and Security Center
Protecting 60+ million identities requires robust security and the trust of our customers

Be confident in who you partner with
Our commitment to you
At Saviynt, our mission is to empower enterprises with cutting-edge identity governance and cloud security solutions. We’ve taken our commitment to cybersecurity to the next level by signing the Cybersecurity and Infrastructure Security Agency (CISA) pledge.
In an era where cyber threats are increasingly sophisticated, securing your digital assets is more critical than ever. By aligning with CISA’s principles, Saviynt demonstrates its unwavering commitment to maintaining the highest standards of cybersecurity. Our participation in this initiative ensures that we stay ahead of the curve, providing you with the most robust and reliable security solutions available.
Signing the CISA pledge is more than just a promise—it's a commitment to action.
Saviynt Trust Portal
Secure
Throughout the development and production lifecycle
Compliant
With local, regional, and global regulations and frameworks
Reliable
With an architecture that supports the most complicated environments
Private
So your data is viewable only by you or others you trust
.webp)
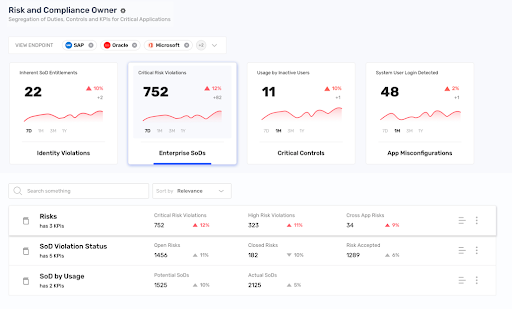
Security
From platform architecture to product development and ongoing operations, security is built into our processes to ensure your data is secure.
- Robust data security and DevSecOps program that includes regular penetration testing by an external third-party
- We leverage our own Enterprise Identity Cloud (EIC) platform and other security tools to manage security
- Mask your instance from the internet without having to take it down in case of advanced threat levels
- Secured and encrypted communications to managed endpoints
Security Bulletins
Saviynt provides important information about security vulnerabilities or misconfigurations that may affect certain products or services. We will provide this information through Security Bulletins, which are made available to all consumers. These bulletins will provide context around the issue, remediation strategies, and other pertinent updates. With a focus on Transparency, such bulletins may be issued even when there is no impact to our customers, or when no action needs to be taken on the part of customers, and in such cases serve purely as informational updates to our customers. Saviynt is now a recognized CVE Numbering AUthority (CNA), recognized by MITRE, and Saviynt will follow the CNA rules outlined by MITRE. Security Bulletin updates will be shared in this section as they become available see below.
Compliance
We adhere to global security standards and regulations and are audited by independent third parties. Core certifications & attestations include SOC 1 and 2 Type II, ISO 27001:2013, ISO 27017:2015, and PCI-DSS.
We are the only SaaS-based, converged identity platform FedRAMP Moderate authorized for IGA and PAM.
ISO27001:2013
ISO 27017:2015
SOC 1 and SOC 2 Type II
FedRAMP Moderate
PCI-DSS
 Saviynt is ISO27001:2013 certified. The standard outlines the requirements for an information security management system (ISMS). Certification attests to Saviynt’s ISMS based on international best practices for security management and controls.
Saviynt is ISO27001:2013 certified. The standard outlines the requirements for an information security management system (ISMS). Certification attests to Saviynt’s ISMS based on international best practices for security management and controls.
 ISO 27017 certification acknowledges that Saviynt has addressed cloud-specific information security threats. The certification attests that services have met best practices for cloud service providers and cloud service customers.
ISO 27017 certification acknowledges that Saviynt has addressed cloud-specific information security threats. The certification attests that services have met best practices for cloud service providers and cloud service customers.
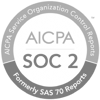 Saviynt has met validation that our security controls are in accordance with the American Institute of Certified Public Accountants’ Trust Services Principles and Criteria.
Saviynt has met validation that our security controls are in accordance with the American Institute of Certified Public Accountants’ Trust Services Principles and Criteria.
 As of July 2022, Saviynt is still the only cloud-based IGA and PAM provider that meets the FedRAMP Moderate requirements for controlled unclassified information in federal government agencies.
As of July 2022, Saviynt is still the only cloud-based IGA and PAM provider that meets the FedRAMP Moderate requirements for controlled unclassified information in federal government agencies.
 In support of customers who process and store payment card data, Saviynt maintains PCI-DSS certification in alignment with the requirements set by the PCI Security Standards Council.
In support of customers who process and store payment card data, Saviynt maintains PCI-DSS certification in alignment with the requirements set by the PCI Security Standards Council.
Privacy
You have control over who sees and has access to your data. Our compliance program aligns with internationally recognized frameworks and data privacy/processing regulations.
- Multi-tenant foundation ensures data across customer environments is never shared
- Data residency in 25+ regions around the world
- Administrator controls within the platform, including for third-parties
- Ability to bring your own keys with you
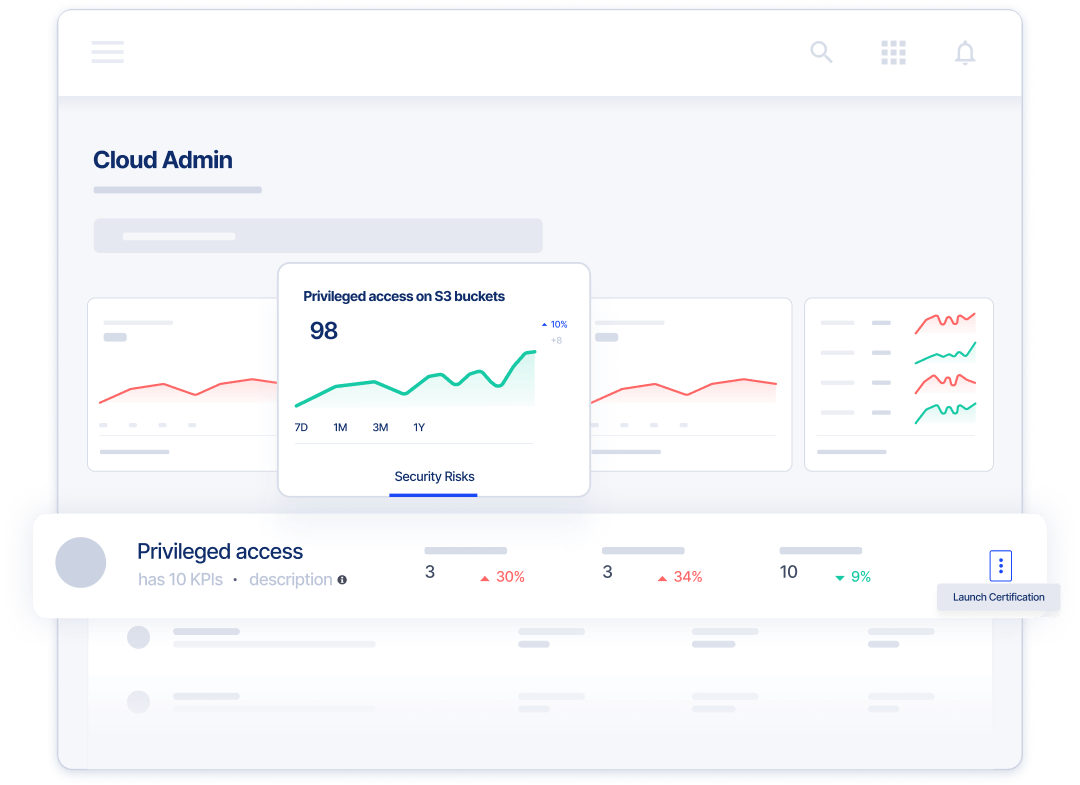
Reliability
Saviynt’s cloud-based infrastructure is designed for elasticity and maximum uptime with built-in redundancy. The platform scales on demand, reduces latency, and increases reliability.
- Distributed application architecture for resiliency in the face of natural disasters or system failures
- Each service on the platform is monitored for operational effectiveness and availability
- Formal business continuity and disaster recovery program with multi-regional recovery capabilities to ensure availability
- Full data, network, and service tenant isolation with auto-scaling to maximize performance and eliminate throttling
A Converged Identity Platform You Can Trust

SOC 1 Type II Audit Report

ISO 27001:2013
SOC 2 Type II Audit Report

ISO 27017:2015

FedRAMP Moderate

PCI DSS Certified
Report a
Vulnerability
To report a vulnerability, please email security@saviynt.com with “Security Vulnerability” in the subject line. To ensure a timely review of the vulnerability, please include supporting material, including steps on how to reproduce the issue. This will help us better understand the nature and severity of the vulnerability.
We will keep you apprised of our efforts in investigating and remediating your concern. When the investigation is complete, we will deliver the results of our findings to you, along with a resolution plan.
We do not allow active penetration, attacks, or audits of our infrastructure through manual or automated means.