What is Zero Standing Privilege (ZSP)?
What is Zero Standing Privilege (ZSP)?
Zero Standing Privilege (ZSP) is a target state of limiting access as much as possible to critical information systems by applying Zero Trust principles to problems in privileged access management. Created by the analyst firm Gartner, ZSP represents the shift from traditional privilege management where account access was “always on,” to granting access to privileged resources for a limited time only, on the basis of need. The traditional “always-on” model presents a security risk and makes your systems prone to attack. In the ZSP model, each access request is decided according to predetermined policies or criteria based on behavioral analytics.
Zero standing privilege embraces the Just-in-Time (JIT) access model. It’s referred to as “Just-in-Time” because users can quickly get access to needed resources. This improves productivity by eliminating the need to prearrange accounts or go through a lengthy approval process.
The Zero Trust model requires that privileged access be granted for a limited time only, with just enough access for the task at hand. Zero Trust combines ZSP with the intelligent context-based decision-making that takes place every time a user or application submits an access request. It enables organizations to secure identity as the new perimeter and prepares them to defend modern infrastructures against today’s threats.
What is Standing Privilege?
Standing privilege is the concept of granting administrative privileges to accounts on a permanent basis. In the age of the cloud, standing privilege is no longer viable. The cost and complexity of managing and protecting standing privilege credentials in today’s cloud environments are simply untenable. Zero Trust and Zero Standing Privilege eliminate the risk involved in standing privilege by eliminating always-on privileges, leading to cost savings and better protection.
Zero Standing Privilege (ZSP) vs Least Privilege
Least privilege says that users should only have access to the required resources needed to complete a job (rather than being granted access to the entire network or large portions of it). Least privilege minimizes risk because it limits the damage done if the user becomes compromised or malicious.
Implementing least privilege is challenging when users are dynamic, moving from one role to another, from one team to another, over time. They need resources for one job that they no longer need in the next. This is where time-limited access comes in. If privileged access is automatically eliminated after a period of time, permissions won’t linger off the radar, and access management becomes less cumbersome.
Least privilege is the standard, and Zero Trust is the ideal. Zero standing privilege, which targets a state of no privilege existing, is a means by which organizations can achieve it. To move to a Zero Trust model, privileged accounts must be eliminated. Even for admins — admin credentials can be hacked and the damage can be substantial. Every access request must be evaluated to ensure it’s appropriate for the user’s current roles and responsibilities. And it should be time-limited to prevent unnecessary permissions. Zero standing privilege is a practical way to give users access to the exact resources they need, just for the specific period of time required.
Why Zero Standing Privilege (ZSP) Matters
Providing time-limited access to resources allows permissions to automatically revert to a secure state after the task at hand is completed. This has several primary benefits:
- Administrators no longer need to remember to lock down once the privileged work is done, reducing insider threats.
- If credentials are compromised by an outside attack, the scope of the damage is limited.
- Compliance requirements are met automatically by tracking when access is granted and revoked.
Securing your user access with standing privilege worked well when everyone was using on-prem servers and VPNs. But now that networks are in the cloud, standing privilege creates undue risk. Employees with privileged access can become insubordinate or fooled by phishing attacks. And hackers can steal credentials more easily with advanced technology and constantly-changing methods. The problem isn’t a small one — 74% of today’s data breaches involve compromised privileged access credentials.
A Zero Trust approach solves this issue by eliminating standing privilege. No one has automatic trust. Every user (human and non-human) must request privileged access each time they want into a system, database, or application. And access is only granted on a time-limited basis. As a result, Zero Trust significantly reduces the damage that access violations can cause.
When threats arise, Zero Trust security architecture is the approach to protect your assets. For example, if an angry employee decides to look for customer data they shouldn’t have, their just-in-time/just-enough access privilege won’t allow them to leave the perimeter assigned to their identity. Additionally, repeated access requests and excessive data collection attempts are likely to flag the behavior as out-of-the-ordinary or risky. But external attacks make up the bulk of breaches — in fact, according to the Verizon 2020 Data Breach Investigations Report, 55% of data breaches involve financially-motivated organized crime. When a hacker or malware like CryptoLocker attempts an attack using compromised credentials, an automated, AI-driven system based on Zero Standing Privilege will immediately flag the request and block access. Even if a nefarious actor does gain access using active credentials, minimal damage occurs because access is limited.
Saviynt & Zero Standing Privilege (ZSP)
Saviynt’s Identity Cloud platform helps ease the move to the Zero Trust Model by drawing the perimeter at identity. Identity-centered solutions provide a foundation for Zero Trust. Zero standing privilege, in-depth visibility, automation, and centralized, continuous monitoring are crucial pieces of Zero Trust.
Saviynt’s Privileged Access Management solution specifically manages JIT access and enforces least privilege, moving you towards the ideal of Zero Standing Privilege.
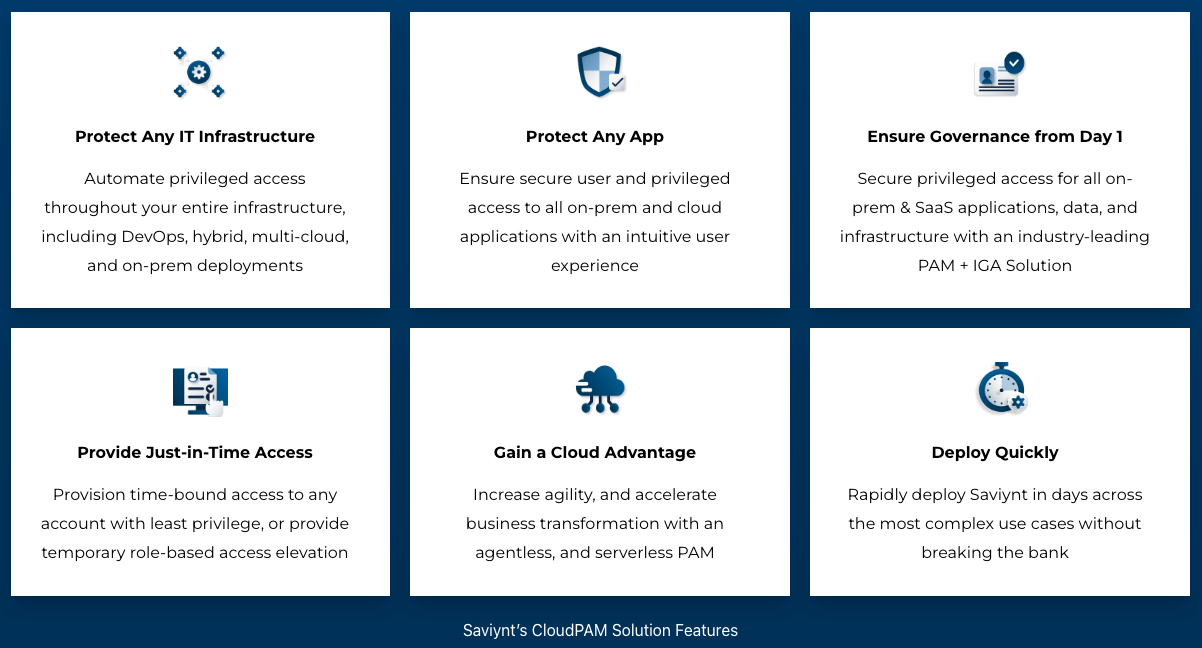
Here are some other features related to Zero Standing Privilege you can leverage with Saviynt:
- Explore an intelligent identity perimeter
- Achieve Zero Standing Privileges with Just-in-Time Privilege Elevation and time-bound access
- Simplify and streamline dynamic access management with “right-sized” access
- Gain complete control and visibility through continuous risk assessment
- Prevent data breaches and insider threats with real-time insights
- Support multi-cloud and hybrid infrastructure
Check out our Deep Dive into Zero Trust video below to learn more about how Saviynt enables your organization to take a Zero Trust approach and enforce Zero Standing Privilege.
Resources