What is a Converged Identity Platform (CIP)?
What is a Converged Identity Platform (CIP)?
A converged identity platform is a software solution that combines multiple identity solutions into one cohesive platform. The most commonly converged solutions include those that address Identity Governance and Administration (IGA), and Access Management needs. These platforms also may include solutions for Privileged Access Management (PAM), Vendor Access Management (VAM), and Governance, Risk, and Compliance (GRC).
Traditionally identity & security teams have implemented separate identity management solutions to achieve security and compliance goals. By combining multiple identity solutions into a singular platform, users can benefit from a singular user experience, greater visibility, automation, and other features that leverage the interoperability between the systems.
Why Do Enterprises Need a Converged Identity Platform (CIP)?
Securing your organization’s digital assets and data has grown increasingly complicated in the modern era. Today’s hybrid infrastructure, work-from-anywhere workforces, and third parties (contractors, partners, vendors, and suppliers) depend on access to critical applications, assets, and data spread across numerous on-premises and cloud-based IT ecosystems. Providing the right levels of access and administration while maintaining compliance with a changing regulatory landscape has become increasingly complex for enterprise security teams.
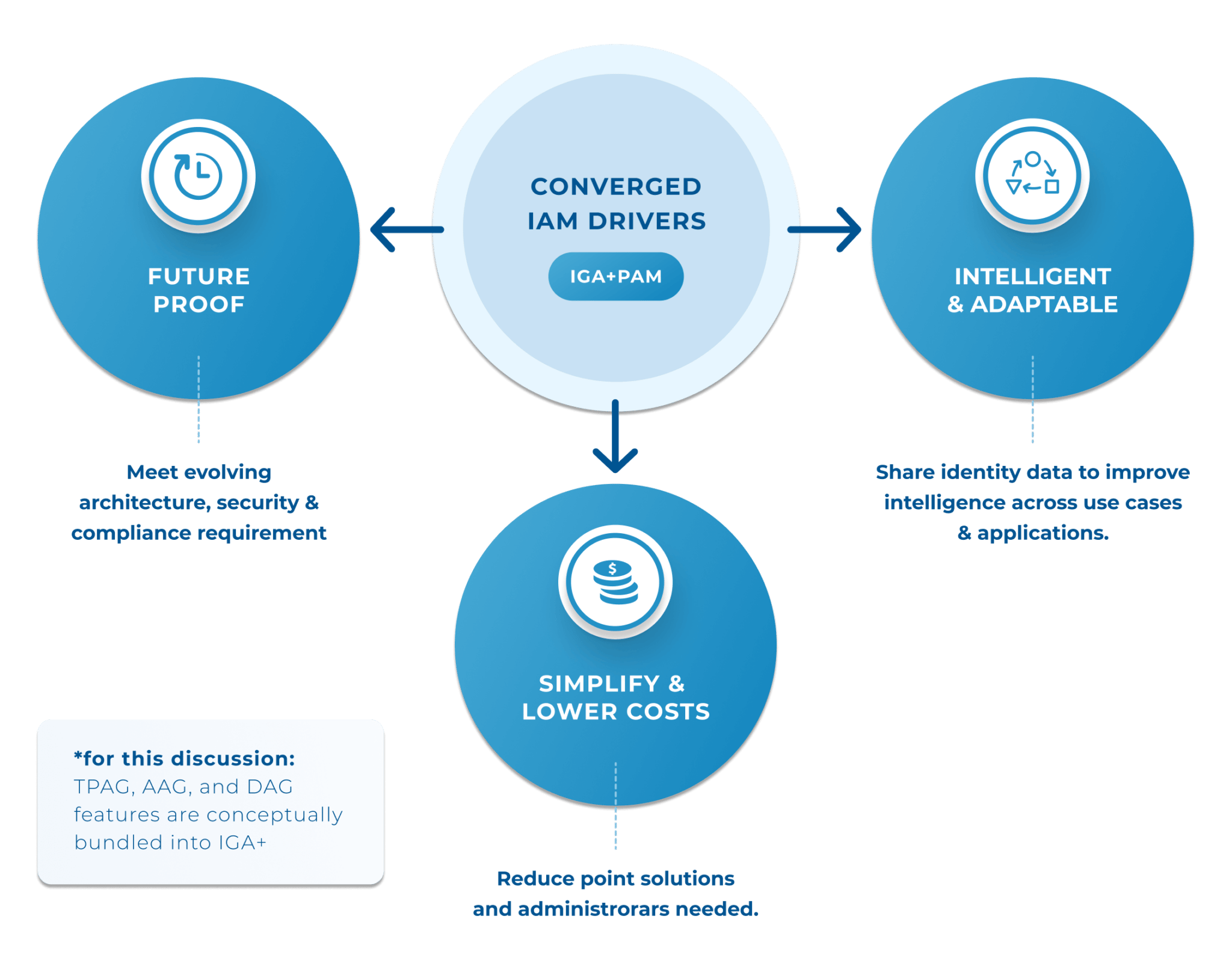
Converged identity platforms simplify implementation and management by reducing the need for multiple-point solutions and their associated costs. These solutions provide deeper visibility, intelligence, controls, and automation across identity ecosystems to quickly detect and mitigate identity-related risks — and ensure continuous regulatory compliance.
Centralize Security Intelligence and Drive Smarter Access Decisions
CIPs allow for the synchronization of data from multiple security tools, centralizing information in a single dashboard so security teams can make informed decisions and mitigate risks. Some common features include:
- Sync activity & access logs with other access and cybersecurity tools
- Monitor and report on activity with deeper context
- Improve threat detection and response times
- Act on risk insights throughout an identity’s entire lifecycle
Lower Costs
There are a number of ways that CIPs lower costs for organizations. The automation of application access provisioning, segregation of duties, and application access reviews eliminate previously manual and time-consuming processes. Employees and contractors can now be onboarded more quickly, and there’s less need for coding talent.
Reduce Reliance on Point Solutions
CIPs enable organizations to move away from multiple-point solutions for IGA, AM, and PAM, to name a few. This consolidation of solutions allows for more efficient workflows and a better user experience, making it easier and faster to implement, manage, maintain, and update/upgrade solutions over time. This greatly reduces the governance and administration burden on security teams.
Accelerate the Move to Zero Trust
Converged identity platforms are also designed to help organizations move toward Zero Trust security models. Zero Trust, also known as least privileged access, accelerates secure digital transformation and protects workforces and modern IT environments through continuous authentication policies and granular access controls, preventing unauthorized access or lateral movement across systems.
Gartner predicts that by 2025, converged identity and access management platforms will be the preferred adoption method for access management, identity governance & administration, and privileged access management in over 70% of new enterprise deployments, driven by more comprehensive risk mitigation requirements (Source: Gartner 2021 Magic Quadrant for Access Management).
Resources

Identity Security Converged: Expert Insights from Top International Brands