Modernization Strategies
Current federal physical infrastructure is crumbling. In fact, it wasn’t built to last in the first place. Below are three key strategies to help realign federal agencies with modern-day security standards.
Move Quickly – and Securely – to the Cloud
Agencies need to invest in modernization programs focused on migrating outdated infrastructure to the cloud. But they need to be thoughtful about their migration processes, as simply copying applications and systems straight to the cloud won’t work. Transferring these applications in the wrong way – via a “lift and shift” strategy, for instance, where an application is copied as-is to a different environment without a redesign – only ends up transferring legacy problems to new environments. Besides, it’s also dangerous, as these types of copy-paste methods just create new opportunities for attackers.
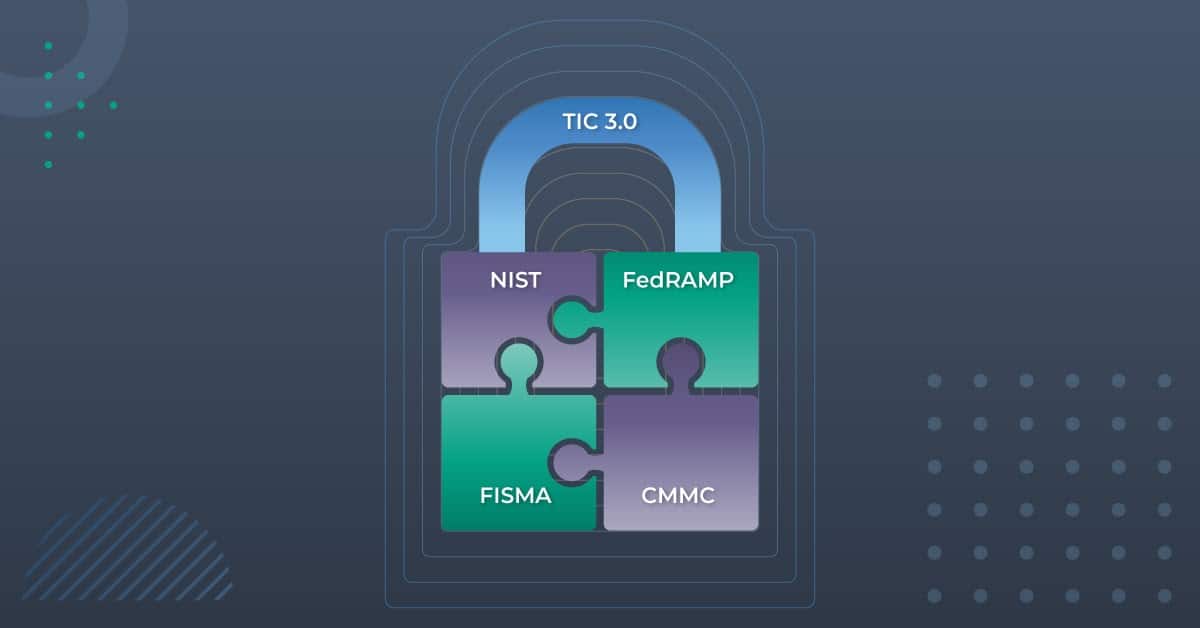
But even after updating to traditional cloud infrastructure, there’s still more work to do. One size does not fit all, and solutions need to be tailored to specific circumstances. Working with an agency such as the Federal Risk and Authorization Management Program (FedRAMP) can help streamline the adoption of new technologies, especially cloud solutions, to help government agencies modernize quickly, securely, and efficiently. So far, FedRAMP has authorized 220 federal organizations, with 54 in the works.
Consider Vendor Management Solutions
When implementing security solutions, think beyond your immediate organization: it’s not just your full-time employees who need access to systems and data. Numerous contractors, subcontractors, and vendors are a part of federal organizations, and overseeing their access is a daunting task – especially if your third-party turnover is high. Vendor access management (VAM) solutions help oversee the entire vendor access lifecycle. These tools not only provide the required access, but they also make sure to keep permissions airtight, restricting anything more than what’s absolutely necessary.
Make Identity Solutions the Backbone of Your Security Strategy
Modern identity solutions can help the government manage access and implement existing compliance needs while quickly adapting to new regulations and mandates. For greater security, consider identity solutions. Identity forms the baseline of a Zero Trust architecture, which has a “default-deny” state. Through zero standing privilege, the principle of least privilege is implemented in a manner consistent with the Biden order guaranteeing that extraneous access is removed.
Zero Trust architecture helps organizations start with the assumption that all access – including internal “trusted” access – should be verified. Systems attempting to connect should be restricted from the very first step, even disallowed from presenting their credentials to one another. A modern identity solution can streamline processes, making managing access more efficient, more secure, and much less time consuming.