SAP Identity Security and Business Application Risk Management Are at an Inflection Point
.png)
Leading the Shift to Identity-Driven Risk Management
Enterprise risk no longer lives within a single application. It spans business systems, cloud platforms, and infrastructure, where access and activity combine in ways that are difficult to see and control.
This shift is changing how organizations approach access, governance, and risk, as reflected in the 2026 KuppingerCole Analysts Leadership Compass reports, where Saviynt is recognized as an Overall Leader in both SAP Access Control and Business Application Risk Management, with top positioning in Innovation.
Key takeaways
At a high level, these reports highlight several important shifts in how enterprise risk is evolving:
- Enterprise risk spans applications, infrastructure, and identities and now requires continuous, cross-application visibility and control.
- Identity is the control plane for enterprise risk, governing access and activity across the ecosystem.
- Traditional approaches based on controls and periodic reviews are no longer sufficient to manage modern enterprise risk.
- As environments expand, risk includes non-human identities, automated processes, and AI-driven activity that must be governed consistently.
- Saviynt is recognized by KuppingerCole as a Leader in SAP Access Control and Business Application Risk Management, with top positioning in Innovation.
Together, these trends signal a fundamental shift: enterprise risk must be managed continuously across applications, infrastructure, and identities, not through isolated controls or periodic reviews.
Analyst recognition is the result. The market shift is the story.
This recognition goes beyond category leadership.
These reports reflect a fundamental shift in how enterprise risk is understood. SAP Access Control has traditionally focused on governance within a single application, while Business Application Risk Management expands that scope to risk across interconnected systems (e.g., Oracle, Salesforce, Workday, Dynamics).
Risk is no longer isolated within a single system and instead, it spans applications, infrastructure (e.g., Azure, AWS, GCP), and identities, where access and activity combine in ways that are difficult to detect. This includes cross-application scenarios such as Separation of Duties conflicts, where risk emerges across systems rather than within one.
Enterprise environments are increasingly shaped by non-human identities, automated processes, and AI-driven activity. Recognition across both categories reflects not only depth within SAP, but the ability to manage risk across the broader enterprise. It reinforces the need for a continuous, enterprise-wide approach that provides visibility and control across the ecosystem.
The patterns behind the shift
Across these reports, KuppingerCole Analysts highlights a consistent pattern: traditional approaches to access governance are struggling to keep pace with modern enterprise environments.
Organizations operate across applications, cloud platforms, and infrastructure, where access is distributed and constantly changing. Siloed tools and application-specific controls create blind spots, limiting visibility into how risk forms across systems.
Cross-application risk is difficult to detect when access is evaluated within individual systems. For instance, Separation of Duties conflicts often span multiple applications (e.g., procurement and payment systems), creating fraud risks that neither system can detect independently. Most tools also lack the visibility to identify these risks in context, and periodic certifications provide only a snapshot view that is likely to be outdated.
As environments become more dynamic, access is continuously created, modified, and used, and organizations have found point-in-time controls insufficient. These risks increasingly include non-human identities, automated processes, and AI-driven activity.
These trends point to a clear conclusion: organizations need a more integrated approach that provides continuous visibility, contextual analysis, and consistent control across applications, infrastructure, and identities.
Where traditional approaches fall short
While the need for more integrated risk management is clear, many organizations remain constrained by approaches that weren’t built for today’s environments.
Most solutions still evaluate access in isolation within individual systems, without visibility across applications, infrastructure, and identities. This leads to fragmented governance, reactive processes, and an incomplete view of enterprise risk.
Even where controls are well defined, they are often applied without the context needed to understand how access combines across systems or how it is actually used. As a result, organizations enforce policies without fully understanding the risk they are managing, such as approving access that appears compliant in one system but creates risk in another.
Many approaches also lack the breadth required for modern environments. Managing enterprise risk requires capabilities beyond traditional access control, including identity security posture management, privileged access management, and governance for non-human and AI-driven identities. Without this coverage, organizations are left with gaps in visibility and control.
Addressing this requires a converged platform and a new model, where identity serves as the control plane for visibility, analysis, and action across the enterprise.
Why analysts recognize Saviynt as a leader
As organizations confront the limitations of traditional, control-centric approaches, the capabilities required to manage enterprise risk are evolving. This is reflected in how KuppingerCole Analysts evaluates solutions across SAP Access Control and Business Application Risk Management.
Analysts emphasize managing access and risk across a broad, interconnected application landscape, including SAP, non-SAP applications, cloud platforms, and hybrid environments.
“Comprehensive entitlement management and Segregation of Duties (SoD) governance across multi-vendor environments”
— KuppingerCole, Business Application Risk Management Leadership Compass (2026)
Saviynt is recognized for delivering this breadth of capability while maintaining depth across key areas. These capabilities are essential for identifying and mitigating risk that emerges across systems, rather than within a single application.
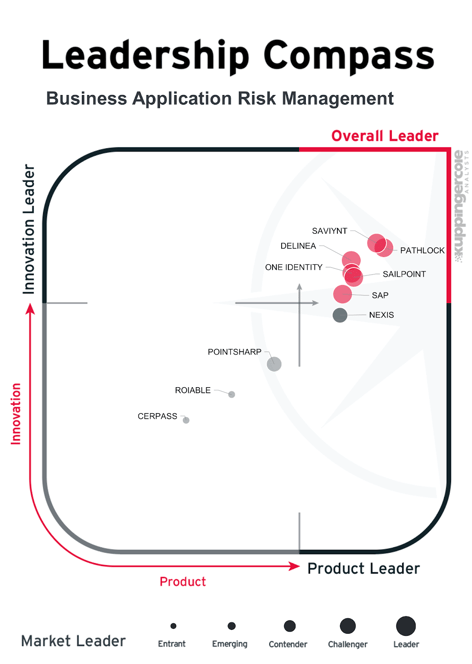
Figure: KuppingerCole Leadership Compass for Business Application Risk Management (2026)
Key capabilities highlighted in the report include:
- Cross-application risk visibility, including Segregation of Duties analysis across multiple systems
- Comprehensive entitlement management across SAP and non-SAP applications
- Support for hybrid and multi-cloud environments
- Advanced analytics and automation for identifying and prioritizing risk
- Unified governance across human and non-human identities
- Integrated approach to access and risk within a single platform
Analysts also highlight the growing importance of automation, analytics, and machine learning to improve how access is governed and risk is identified.
“Integrating automation and advanced analytics to streamline operations and compliance activities”
— KuppingerCole, Business Application Risk Management Leadership Compass (2026)
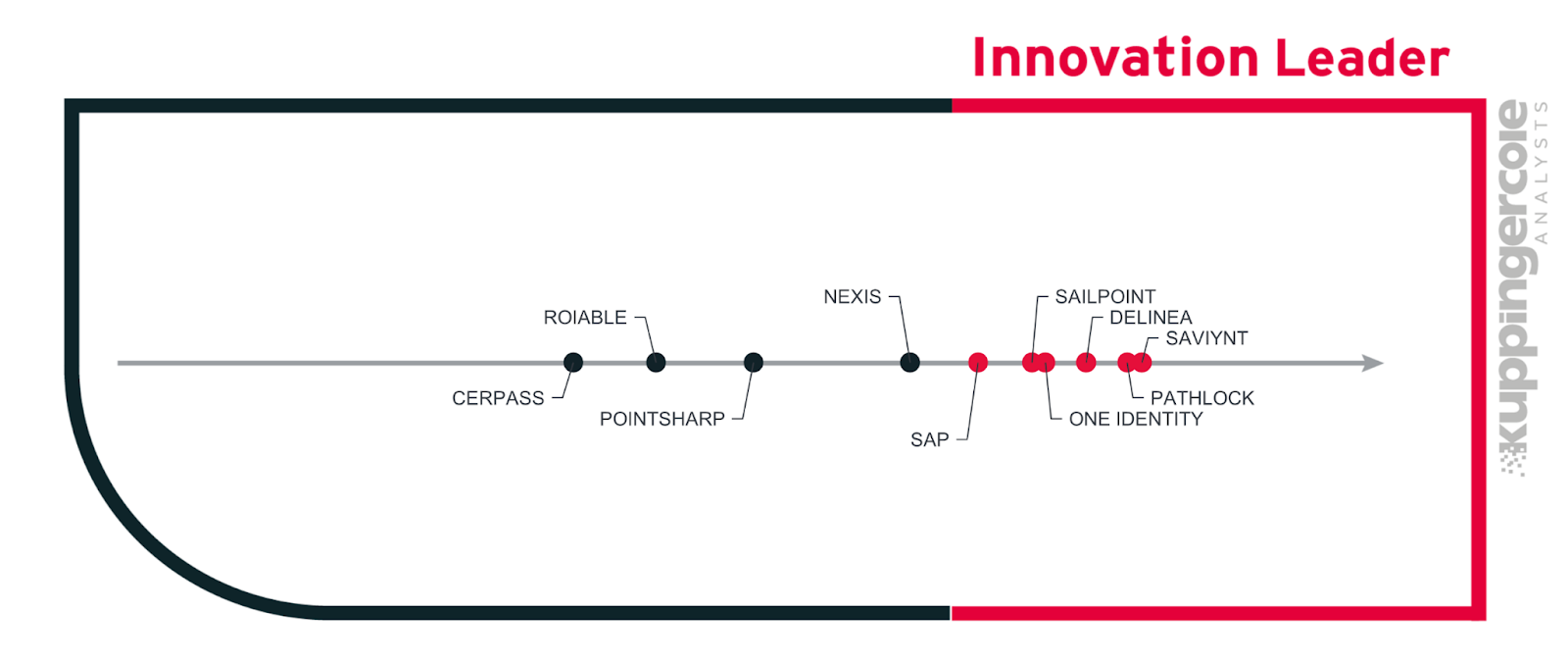
Figure: KuppingerCole Innovation Leadership (2026)
These capabilities support a shift from static controls to more dynamic, continuous approaches to risk management, reinforcing the need for solutions that extend beyond SAP to manage access across a broader range of applications.
Underlying these strengths is a broader architectural advantage. By bringing together identity governance, application access control, and risk intelligence into a unified platform, Saviynt delivers the coverage and contextual understanding required to manage risk across the enterprise.
Where Saviynt goes further
While some focus on extending coverage within the traditional paradigm, the reality is that addressing today’s challenges requires much more than extending controls across systems. Saviynt provides a fundamentally different model for managing enterprise risk across the enterprise.
Saviynt treats identity as the control plane for managing risk across the enterprise, providing a unified view of access, activity, and entitlements across applications, infrastructure, and identities.
This enables organizations to move beyond detecting violations to understanding how risk forms across systems and acting on it continuously. Cross-application scenarios such as Separation of Duties conflicts illustrate this, where risk emerges from the combination of access across systems and requires a unified, contextual view to be identified and addressed.
As identity evolves, this model becomes even more critical. Modern environments include not only human users, but also non-human identities, automated processes, and AI-driven activity operating across systems.
Managing enterprise risk requires capabilities beyond traditional access control. Identity security posture management, privileged access management, and governance for non-human and AI-driven identities must work together as part of a unified approach.
By converging identity governance, application access control, privileged access, and risk intelligence into a single platform, Saviynt enables a continuous, enterprise-wide model for managing risk across applications, cloud platforms, and infrastructure. This allows organizations to analyze access and activity in context and act in real time.
The result is a shift from reactive, control-based governance to a proactive model where organizations can understand, prioritize, and reduce risk across the enterprise.
What this means for organizations
For many organizations, the challenge is no longer simply enforcing access controls. It is understanding how risk forms across systems, how it evolves, and how to act before it results in audit findings, fraud, or operational disruption. This shift has direct implications across the business.
For finance and risk leaders, it means moving beyond periodic reviews to continuous visibility into access and activity across critical systems, enabling stronger proactive controls and greater confidence in audit outcomes.
For internal audit teams, it means reducing reliance on manual processes and point-in-time assessments, improving audit readiness, and accelerating remediation.
For security and IT leaders, it means addressing identity-driven risk across applications, infrastructure, and non-human identities, with consistent governance and real-time insight.
While these outcomes serve different stakeholders, they are driven by a common need for unified visibility, contextual understanding of access, and the ability to act on risk continuously. This represents a shift from fragmented governance to a continuous, enterprise-wide model, enabling organizations to move from reactive controls to proactive risk reduction.
Leading the shift to identity-driven risk management
The recognition of Saviynt as a Leader in both SAP Access Control and Business Application Risk Management by KuppingerCole Analysts reflects more than strong capabilities. It highlights a broader shift in how organizations approach access, governance, and risk.
As enterprise environments expand across applications, infrastructure, and identities, managing risk requires a unified, continuous, and context-driven approach. Organizations that rely on fragmented tools and periodic processes cannot keep pace with the complexity and scale of modern environments.
In contrast, a converged, identity-centric model defines how enterprise risk is managed, enabling better decisions, stronger controls, and more resilient operations.
To explore these trends and see how leading vendors are addressing them, download the 2026 KuppingerCole Analysts Leadership Compass reports on SAP Access Control and Business Application Risk Management.

Report
Saviynt Named Gartner Voice of the Customer for IGA

EBook
Welcoming the Age of Intelligent Identity Security

Press Release
AWS Signs Strategic Collaboration Agreement With Saviynt to Advance AI-Driven Identity Security

Solution Guide
.png)
