We Deliver Enterprise Control Over AI.
Saviynt secures every identity — human, non-human, and AI.
Securing over 100 million identities at global leaders






-1.webp?width=200&height=82&name=webmedium%20PNG-ADS%20logo%20with%20Advanced%20Drainage%20Systems%2c%20Inc.%20Stacked%20-%20Color%20(2)-1.webp)








Swipe to navigate
Empower and protect all your identities
Internal Workforce
Your organization's employees
Learn moreInternal Workforce
Your organization's employees
External Workforce
Your suppliers, contractors, etc.
Learn moreExternal Workforce
Your suppliers, contractors, etc.
Privileged Users
Admins, DevOps, SecOps, etc.
Learn morePrivileged Users
Admins, DevOps, SecOps, etc.
Non-Human Identities
Credentials, accounts, workloads, etc.
Learn moreNon-Human Identities
Credentials, accounts, workloads, etc.
AI & AI Agents
Chatbots, copilots, LLMs, etc.
Learn moreAI & AI Agents
Chatbots, copilots, LLMs, etc.
Recognized market leader in identity security by top analysts

Saviynt Named a 2026 Customers' Choice in Gartner® Peer Insights Voice of the Customer™ for IGA

Saviynt Named a Leader in Frost Radar™ for Non-Human Identity Solutions 2025

Saviynt Named a Leader in QKS SPARK Matrix™: Privileged Access Management 2025
Identity Security for AI.
AI for Identity Security.™
Our AI-based platform enables you to deliver end-to-end identity security.
For all
identities
Internal and external, workforce, machines, and AI
Across all apps
& platforms
ERP, EMR, SaaS, IaaS, and more
In any
environment
Cloud, on-premises, and hybrid identity security
Unified identity security for the AI era
Implement identity security for AI
Ensure all AI identities are secure, compliant, and trustworthy, no matter where they reside in your organization.
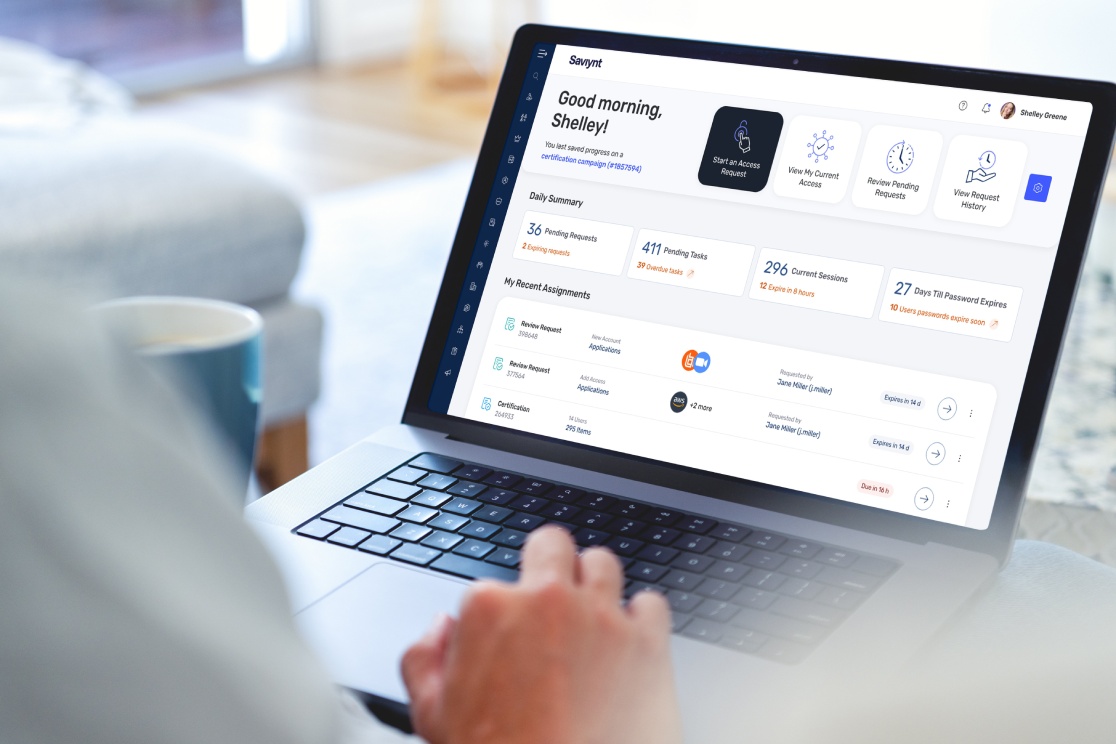
AI that works for you
SaviAI solves the biggest challenges with identity security platforms: cost, complexity, and user fatigue. Powered by Agentic AI, SaviAI streamlines integrations and onboarding with intelligent workflows that reduce operational overhead.
AI agents simplify and automate complex identity security challenges
Transform identity security with agentic AI
Enable every employee to manage access confidently and securely — just by using natural language. SaviAI provides contextual understanding and intelligent guidance, so users can effortlessly navigate complex identity decisions. Gain real-time insights and recommendations to turn identity interactions into a seamless experience: reducing tickets, accelerating productivity, and delivering smarter outcomes across the organization.
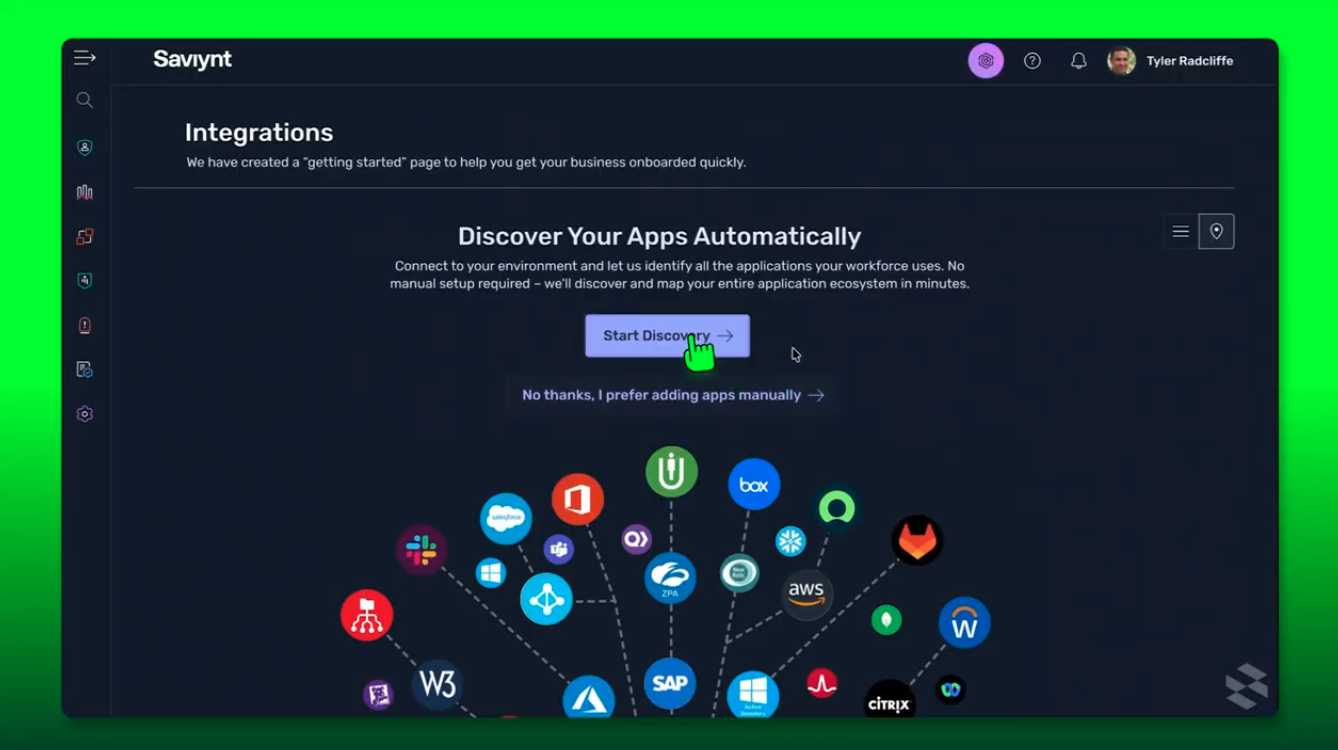
Supercharge app onboarding with AI-driven intelligence and eliminate months of manual effort. SaviAI learns patterns, autonomously configures connections, and brings even the most complex apps online in mere hours. Gain faster time-to-value and dramatically lower integration costs with conversational onboarding, governance, and security. It’s the new standard for identity integration in the age of AI.
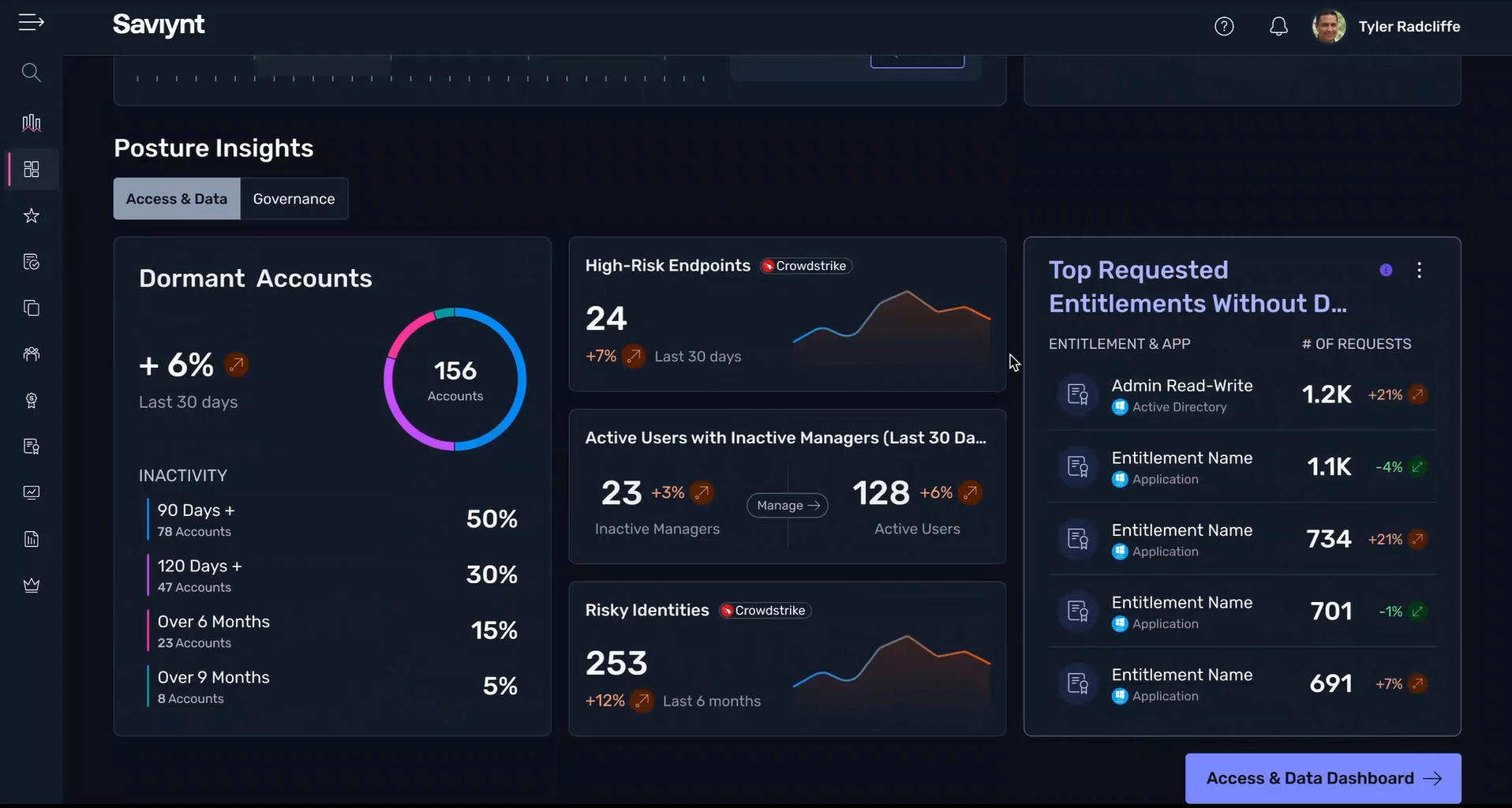
Bring autonomous intelligence to identity-driven security operations — detecting suspicious activity, correlating risk signals, and recommending the right response in seconds. SaviAI provides contextual insights, guides triage, and automates remediation to streamline investigations, contain threats faster, and stay ahead of identity attacks, resulting in faster detection, smarter responses, and a stronger security posture.
Deliver next-gen autonomy to identity administration and precisely execute tasks while prioritizing security and compliance. SaviAI intelligently manages configurations, entitlements, policies, and lifecycle changes, significantly reducing effort and errors. Streamline operations and enforce consistent governance with contextual awareness and built-in guardrails for smarter administration, stronger security, and dramatically improved efficiency.
Identity security for all enterprise applications











A 5x Gartner® Customers' Choice
The only vendor named a Customers' Choice five times for Identity Governance and Administration





Real Saviynt customers, real results
"The difference between Saviynt and other vendors is that, although they are going through rapid growth, it remains personal, so you're not dealing with a department, you're dealing with a person. It's quite a transparent organization, and that helps."
"We needed a platform that would support both our on-premises ERP and cloud applications with equal strength. Saviynt was able to accomplish both very easily."
“Identity governance is critical to UWA’s strategic objective of improving the student experience... Saviynt’s solution will significantly enhance our security, as we will know who has access to data and whether or not that access is appropriate."
Ready to see Saviynt in Action?
“Saviynt has enabled us to modernize our workflows, so that we could consolidate identities on a single platform, eliminate spreadsheets and manual processes, and work towards organization-wide implementation of role-based access controls.“




-1.png?noresize)