Is Your IGA Solution Missing the Mark?
There’s a myth floating around some security discussions.
It suggests that any new solution modernizes identity governance equally. The problem with this belief is that it’s not true. Even in an age of analysts and user reviews, blogs, and buyers’ guides, too many enterprises invest in IAM solutions – cloud or otherwise – that don’t truly revolutionize their approach to compliance & security.
In this blog, we explore what modernization really requires.
We contrast the performance of some of the varied IGA solution styles (like legacy on-prem, multi-app, and the newer “light” platforms) against a full-featured, cloud-first model. Then, we establish why the latter is the only path to comprehensive identity security.
Modernization Must-Have #1
Cloud-Native not Cloud-Lifted
Some legacy IGA vendors simply moved the infrastructure of their solution to the cloud – and call it a cloud-based offering. But this doesn’t actually solve the management challenges that cloud-architected solutions do. So, although buyers no longer require physical, on-premises infrastructure components, the headaches from a legacy model continue. For them, the lifted-to-the-cloud offering adds little improvement.

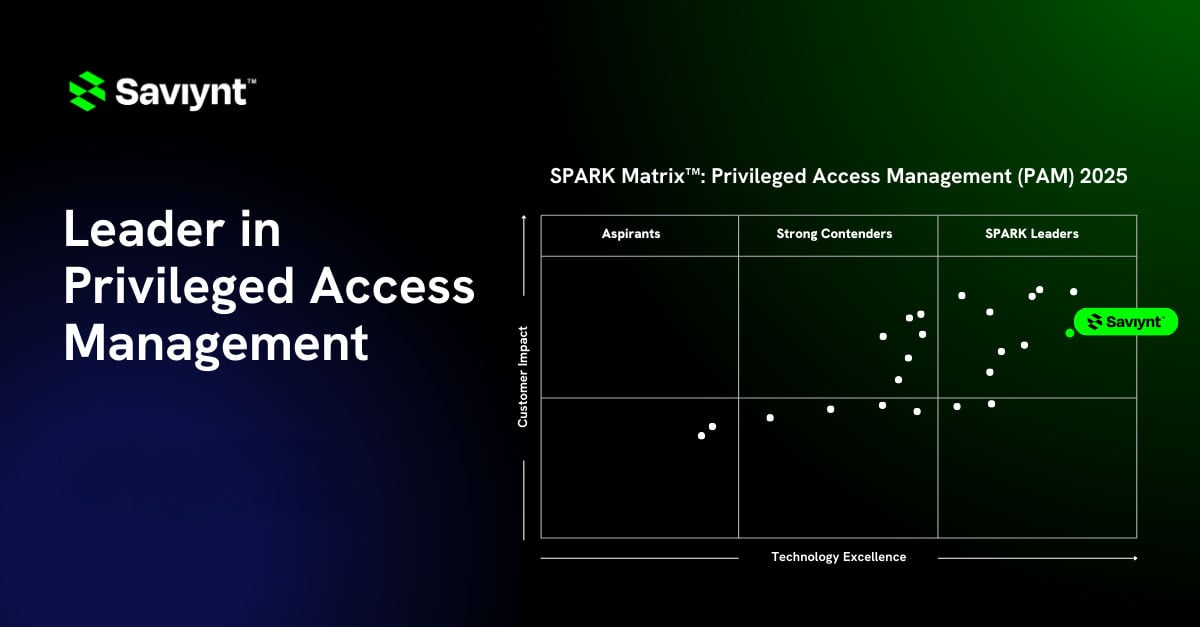
When platforms are simply “lifted” to the cloud, cumbersome architecture and management issues remain. Training and other third-party professional services investments also likely persist, increasing operational costs. So too do limitations for capabilities like integrated PAM. Additionally, these platforms lack the speed and nuance to manage and monitor privileged identity lifecycles. Continuous monitoring is essential to proactive risk management; partial and irregular rhythms won’t cut it.
Unknowingly, security leaders also end up introducing scalability issues (and thorny future upgrade scenarios). On the other hand, full-featured and cloud-native solutions simplify overall management, reducing total cost of ownership and increasing ROI.
Modernization Must-Have #2
Converged and Cohesive not Stitched and Siloed
As enterprises pursue transformation initiatives and migrate to the cloud, they often struggle to support remote workers, manage machine identities, and navigate shifting threat and regulatory landscapes.
This brave new world requires a converged identity platform – one that unites all aspects of identity access and governance. Truly modern IGA relies on unified controls and risk management, contextualized identity risk, advanced analytics, and automated access (and issue remediation).
Many enterprises don’t realize the clear converged difference – and opt for a mix of legacy on-premises tools or a patchwork of cloud-apps. Others target converged solutions, but settle for a piecemealed approach with niche solutions. Either way, if the approach mandates a medley of tools, you convolute security stacks and increase complexity.
The fundamental issue is that enterprises lose seamlessness. Point-based and light tools (even if all cloud-based) generally don’t have workflows around certification campaigns, access requests, and SoD capabilities. They lack the integrations, connectivity, and reporting capabilities that modern business requires.

And instead of simple configuration, complex coding may be needed depending on the makeup of the technology stack. This code is hard to update, so companies grow vulnerable to cyberthreats from issues like siloed identities, machine identities, and access groups.
Only one model provides the multi-dimensional optics needed for a genuinely secure security posture. Converged solutions help normalize data from across the identity landscape. They illuminate an organization’s threat landscape for all identities – regardless of location or type.
Modernization Must-Have #3
Flexible not Flimsy Multi-Cloud Governance
Enterprises often opt for a combination of public clouds or operate hybrid environments for various enterprise applications. This is why a modern approach to identity security revolves around flexibility: A truly transformative IGA solution works easily across varied environments.
To understand the importance of this, consider one governance issue security leaders commonly face:
Most cloud providers have unique models for how identities and privileges get managed. These display different roles and security controls, compromising leaders’ abilities to maintain broad visibility and reduce privileged access sprawl. Weak control or disconnected management weakens security postures.
In a recent report on cloud IGA, KuppingerCole reinforces the flexibility offered by cloud-first identity governance.

The experts agree: no solution model – whether on-prem, platform-light, or a combination of point solutions – has the flexibility of cloud-first.
Plus – a Modernization Bonus!
While I could fill another blog with must-haves, we wrote a buyer’s guide that offers even more guidance. Instead, I’ll leave you with a couple of security treats that enterprises discover when they opt for converged, cloud-based IGA:
- Advanced machine learning with robust analytics: Enterprises reduce resource drain with added automation and a risk-based approach to identity governance processes including intelligent access requests, and event-driven micro-certifications and reporting.
- Hassle-free compliance: Compliance review and management is dramatically simplified with out-of-the-box security controls mapped to regulatory frameworks, with continuous monitoring and real-time remediation.
- Extensive Separation of Duties (SoD) functionality: Leaders deploy pre-built rulesets addressing growing audit requirements – without add-on solutions.
When’s the last time your IGA solutions surprised and delighted you?
The Last Word on Cloud-First
Our cloud-based model is an obvious “SaaS-based platform to replace high cost, siloed applications,” suggests Forbes. Further, they suggest our approach is “… less complex, highly secure, automated, quicker to deploy, and [enables] flexible onboarding and offboarding.”
Enterprises find better value in solutions that support modern workflows, work together, and simplify management. No mix of siloed applications, legacy deployments, or feature-light solutions capture this.
Only the cloud can.